
Top 4 SIM Location Trackers To Easily Find Your Lost Motorola Razr 40 Device

Top 4 SIM Location Trackers To Easily Find Your Lost Motorola Razr 40 Device
Losing your smartphone can be a distressing experience. It’s not just a device; it’s a treasure trove of memories and personal information. Fortunately, technology has come to the rescue with SIM location trackers. These useful tools will help you ensure your lost device is never truly lost.
Whether you call it a SIM location tracker, a SIM card locator, a SIM card finder, or even a SIM card number finder, these smart solutions are your best friends in times of need. So dive in and discover the top 4 SIM location trackers to make device retrieval a breeze.
![]()
Part 1: Why You Need SIM Location Trackers at Your Disposal
In today’s fast-paced world, losing a smartphone happens more often than one would like to admit. Picture this: You’re in a rush, juggling tasks, and suddenly, your phone slips out of your pocket or bag. Panic sets in as you realize it’s nowhere to be found.
![]()
Losing your smartphone can be depressing, not just because of the cost of replacing it. Think about all the photos, messages, and personal information stored on it. It’s like losing a piece of yourself. This is where SIM location trackers come to the rescue.
Common Scenarios of Device Loss
Check out some of the most common scenarios where a phone might get lost:
- Have you ever left your phone in a cab or at a restaurant? It’s surprisingly common.
- Sometimes, it slips out of your pocket during a hectic commute.
- In the worst cases, it might even get stolen.
The Growing Need for SIM Card Finders
With lives deeply intertwined with technology, the demand for easy and effective device tracking is rising. People want solutions that don’t require a tech genius to operate. They want something simple, straightforward, and, as much as possible, free SIM card locators.
Factors To Consider When Choosing a SIM Location Tracker
Now, here are the top factors you need to check when you are about to choose an online SIM location tracker.
- You need a tracker that can pinpoint your device’s location precisely.
- Ensure it works with your device and operating system.
- **User Reviews.**Check what others say about the tracker. Real user experiences matter.
- **Additional Features.**Some trackers offer extra perks like geofencing or remote device control. Consider what suits your needs.
The bottom line is that SIM location trackers offer a lifeline when your device vanishes into thin air. They’re your best shot at getting it back quickly and easily. Plus, in this age of digital privacy, knowing where your personal information is can be a big relief.
In the next part of this journey, this article will delve into the top 4 SIM location trackers that are here to make your life simpler and your devices safer. So, stay tuned and explore these handy tools that bring peace of mind to the palm of your hand.
Part 2: Top 4 SIM Location Trackers
Now that you understand why SIM location trackers are essential let’s dive into the world of these handy tools. This section explores four of the most popular SIM card finder that can help you track your SIM card location online for free.
Hoverwatch
Hoverwatch is your go-to solution for simple and effective SIM location tracking. Designed with user-friendliness in mind, it offers accurate GPS tracking call and SMS monitoring and operates in stealth mode.
![]()
Key Features
Check out Hoverwatch’s essential features below:
- It provides real-time GPS tracking to pinpoint your device’s location accurately.
- You can monitor calls and messages on the target device.
- Hoverwatch operates discreetly, so the user of the tracked device won’t know it’s being monitored.
Pros
Listed below are Hoverwatch’s advantages:
- Easy to set up and use, making it ideal for beginners.
- Supports a wide range of devices and operating systems.
- Affordable pricing plans.
Cons
Below is the drawback of using Hoverwatch:
- Some advanced features may require rooting or jailbreaking the target device.
mSpy
For a comprehensive monitoring solution that includes SIM location tracking, mSpy is a top choice. It not only provides real-time location tracking but also offers geo-fencing and social media monitoring. mSpy is particularly popular among parents who want to ensure their children’s safety online.
![]()
Key Features
Key characteristics of mSpy are as follows.
- Track the target device’s location in real time.
- Set up virtual boundaries and receive alerts when the Motorola Razr 40 device enters or leaves these areas.
- Monitor social media activities and messages.
Pros
The benefits of using mSpy are as follows:
- Excellent for parents who want to ensure their child’s safety online.
- Comprehensive monitoring, including text messages, calls, and social media.
- Compatible with Android and iOS devices.
Cons
The disadvantages of mSpy are outlined below:
- Relatively higher pricing compared to some other trackers.
- Advanced features might require device rooting or jailbreaking.
Spyic
Spyic is a trusted name in the world of monitoring and tracking software. It offers precise location tracking, works without rooting or jailbreaking, and comes with features like geofencing. Spyic is highly reliable, user-friendly, and compatible with Android and iOS devices.
![]()
Key Features
See the highlights of Spyic below:
- It provides accurate location information, including location history.
- Spyic can be used without rooting or jailbreaking the target device.
- Set up virtual boundaries and get alerts if the Motorola Razr 40 device enters or exits these areas.
Pros
Here are some of Spyic’s many benefits:
- Highly reliable and user-friendly.
- Works on both Android and iOS devices.
- Offers a web-based dashboard for easy monitoring.
Cons
The drawbacks of utilizing Spyic are as follows:
- The pricing may be a bit on the higher side for some users.
- Some advanced features may require a premium subscription.
Spyzie
Spyzie is a versatile monitoring tool covering SIM location tracking and more. It provides accurate location updates, social media monitoring, and call/text tracking. One of its standout features is that it doesn’t require complex technical procedures like rooting or jailbreaking, making it accessible to users of all levels.
![]()
Key Features
Take a look at some of Spyzie’s best qualities:
- Get real-time location updates of the target device.
- Track social media activities, messages, and media files.
- Monitor calls and text messages on the target device.
Pros
Spyzie’s benefits are as follows:
- Compatible with Android and iOS devices.
- There is no need for complex technical procedures like rooting or jailbreaking.
- User-friendly interface for easy navigation.
Cons
The Spyzie’s drawback is detailed here:
- Pricing plans might be a consideration for budget-conscious users.
Part 3: How To Unlock iPhone SIM?
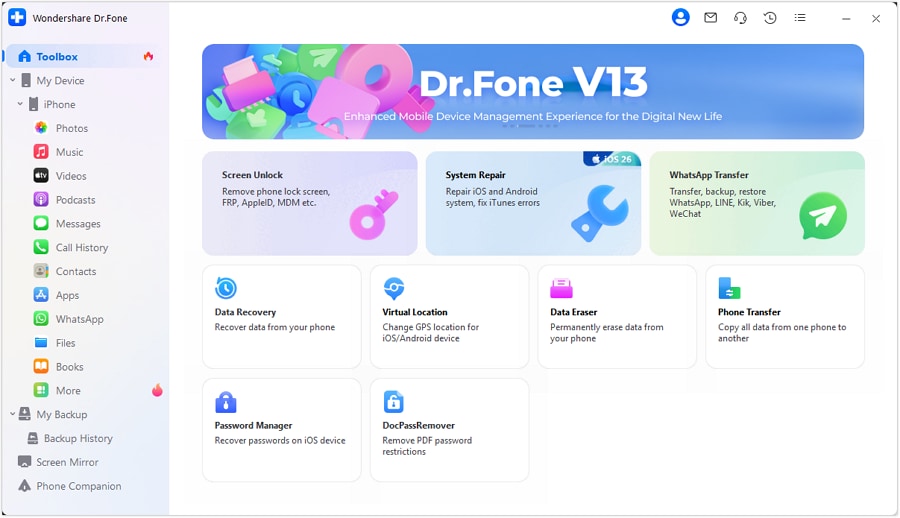
Now, what if you don’t only want to track your SIM number location but also want to deal with other iPhone SIM-related issues like SIM not supported, invalid SIM, locked SIM, or no network servicing? Luckily, this article is also set to share a robust solution - Wondershare Dr.Fone – SIM Unlock. This versatile tool helps you locate your device and ensures your iPhone’s SIM card functions smoothly.
Dr.Fone - Screen Unlock (iOS)
Best SIM Unlock for iPhone.
- Simple, click-through, process.
- Fix SIM unlock with a few clicks.
- Supports almost all carriers, from Vodafone to Sprint.
- No tech knowledge required, everybody can handle it.
- Supports the latest iOS version fully!

4,395,217 people have downloaded it
Why Choose Dr.Fone - SIM Unlock
Below are the key features that make this tool unmatched:
- Dr.Fone - SIM Unlock is your trusted companion for various iPhone models. Whether rocking the latest iPhone or an older version, this tool has your back.
- **User Friendly Interface.**No need to be a tech wizard to use Dr.Fone - SIM Unlock. Its straightforward interface ensures that even if you’re not tech-savvy, you can easily unlock your iPhone SIM.
- **Broad Compatibility.**It supports many iPhone models and is regularly updated to stay compatible with new releases.
- **Quick and Easy.**The process is designed to be simple and efficient, ensuring you get your iPhone back up and running quickly.
Step-by-Step Guide to Using Dr.Fone - SIM Unlock
Here’s a simple step-by-step guide to unlocking your iPhone SIM using Dr.Fone - SIM Unlock:
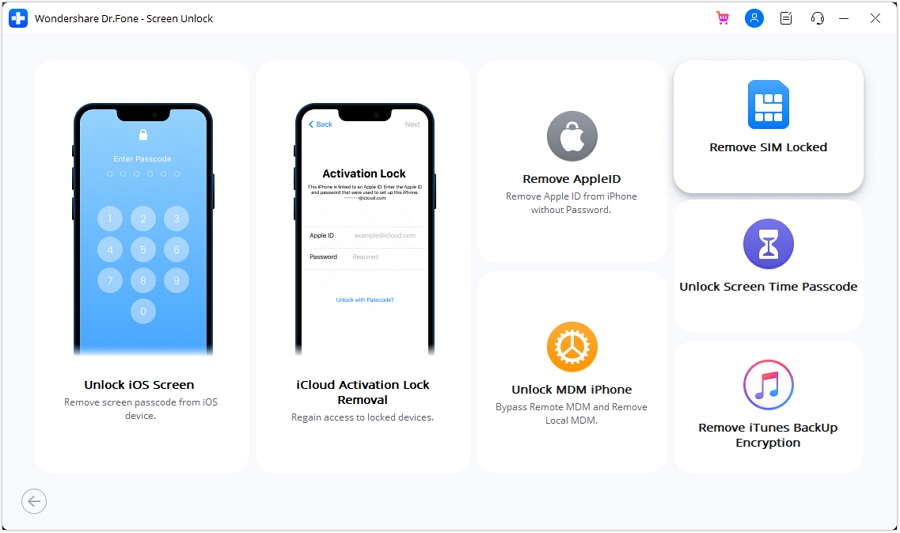
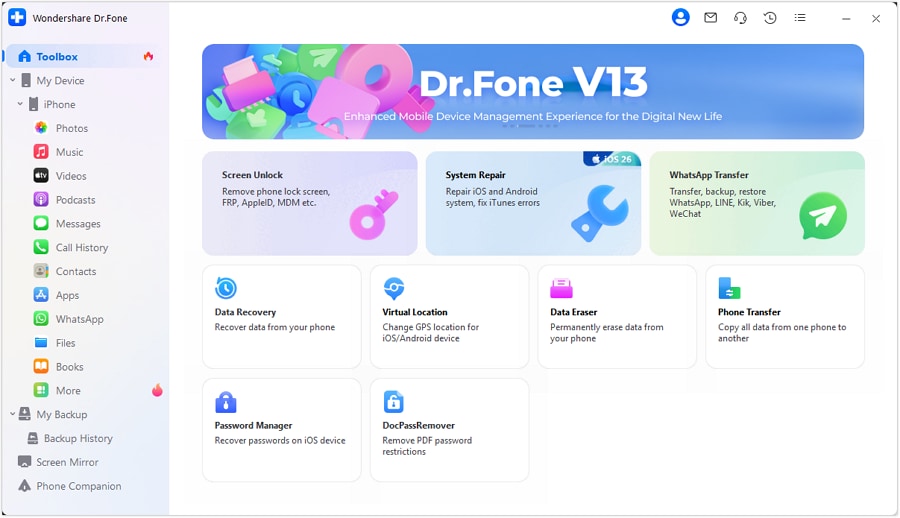
- Step 1: After downloading and installing the software, start Wondershare Dr.Fone on your computer. Continue to the Toolbox area, then select Screen Unlock and iOS to launch the tool in a new window.
- Step 2: In the new window, hit the Remove SIM Locked button to start the process. You will then be sent to the Remove SIM Locks page, where you must click Start to initiate the process.
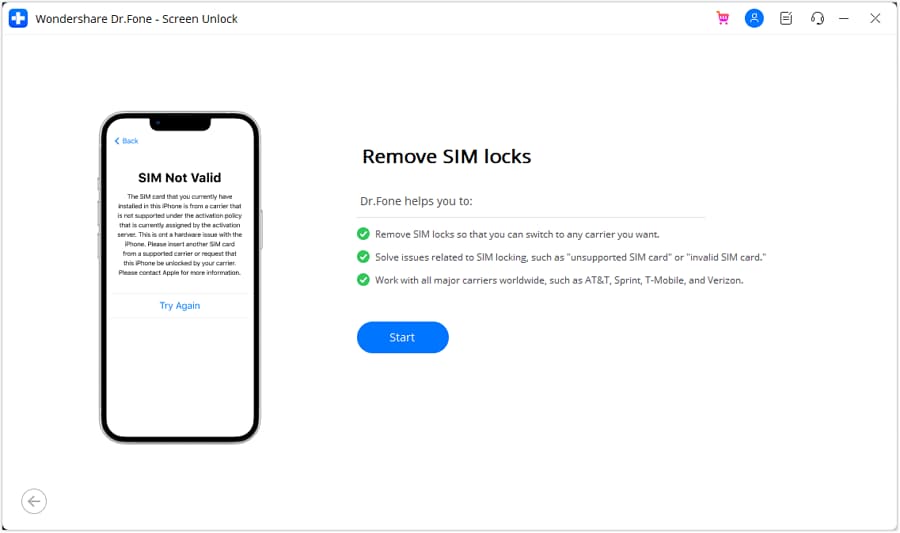
- Step 3: The platform will detect your device and present its details on the following screen. Click the Unlock Now button to continue the unlocking procedure.
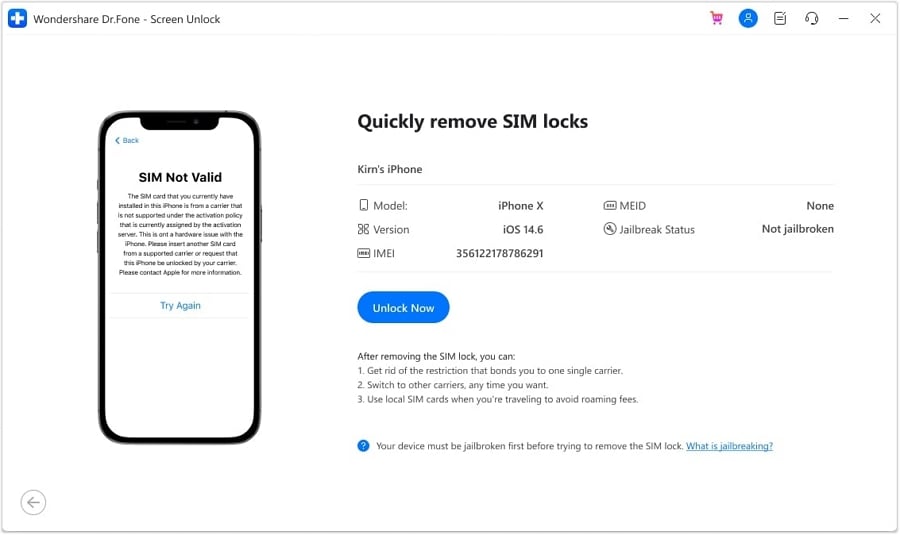
- Step 4: Because this method necessitates jailbreaking your iOS device, you will be prompted to do so first. If you want to follow a guide, click on Jailbreak Guide. If you want to watch a video guide, select Watch Video.
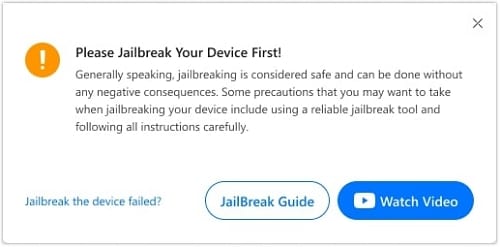
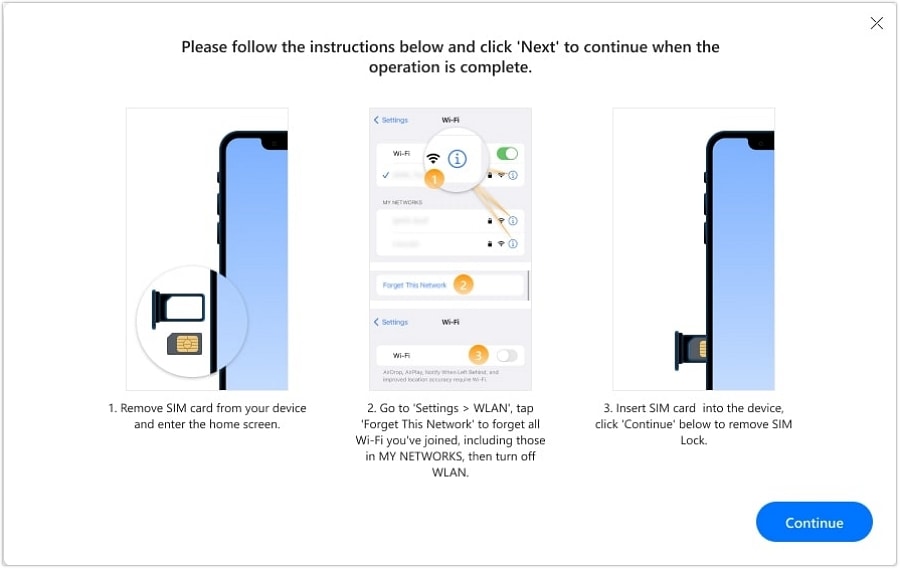
- Step 5: The screen will invite you to perform several actions, starting with removing the SIM card from the iDevice. To access the Motorola Razr 40 device’s network settings, go to Settings, then WLAN. Find the Wi-Fi networks you’ve joined and select Forget This Network.
- Step 6: Unlink all connected networks from My Networks and turn off Wi-Fi. After that, re-insert your SIM card and press the Continue button. The following screen will offer a prompt box with the status of the unlocking process.
- Step 7: After a few moments, the window will display a completion notification, and you must click Done to complete the process.
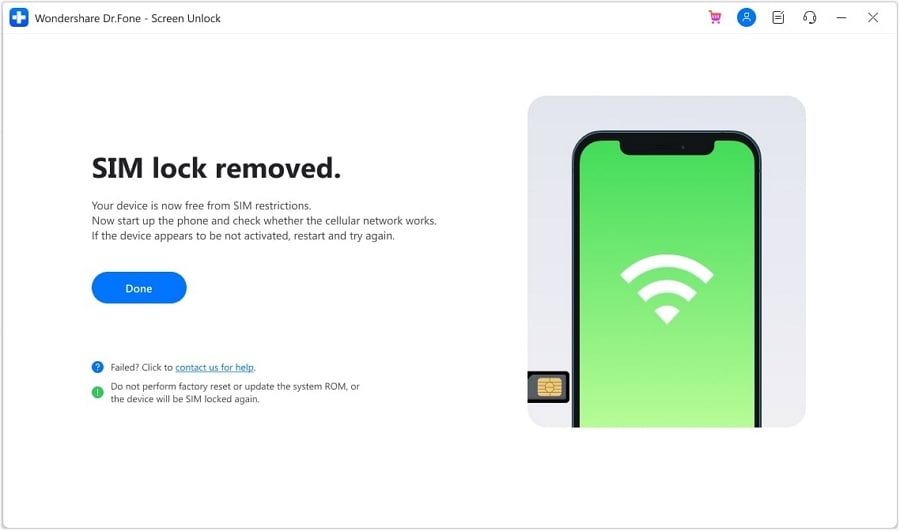
And that’s it! You’ve successfully unlocked your iPhone SIM using Dr.Fone - SIM Unlock. Now, your device should be free from SIM-related issues, and you can enjoy seamless network connectivity. So, if you’re facing SIM woes, don’t fret; Dr.Fone - SIM Unlock has you covered.
Conclusion
Losing your smartphone is more common than you might think. Thankfully, SIM location trackers are here to save the day. These simple tools offer accuracy and peace of mind, ensuring that your lost device can be swiftly recovered. Remember, quick device recovery means safeguarding your cherished memories and personal data. So, explore the recommended trackers this article has covered, and choose the one that best suits your needs.
And if you ever need to unlock your SIM card , Dr.Fone - SIM Unlock is your best companion. Enjoy the enhanced security, broad compatibility, and user-friendliness that come with it.
How to Reset a Motorola Razr 40 Phone that is Locked?
We all have been there when put a tough to crack the lock on the smartphone and forget the password all along. Such circumstances can be tedious at times, but there is a way around it. If you have spent countless hours on how to reset a Motorola Razr 40 phone that is locked, or how to get into a locked Motorola Razr 40 phone quickly with or without Factory Reset. This is the right article for you. Here we will describe all the different ways in which you can reset your phone with the convenience of software to even reset it manually. So, without making further due, let’s jump right into it.
Part 1: What should I be aware of before resetting a Motorola Razr 40 Phone that is locked?
Before you go to reset your locked Motorola Razr 40 phone, it’s crucial to learn about a few key factors. These factors will enable you to make a well-informed choice and help avoid potential complications during the factory reset process.
1. Data Loss
Resetting your locked Motorola Razr 40 phone typically involves performing a factory reset. The process erases all data and settings on the Motorola Razr 40 device. This includes your files, apps, contacts, and other information stored on the phone. You can easily restore these data if you have backed up data before. It’s crucial to back up essential data regularly to avoid data loss.
2. Factory Reset Protection (FRP)
Motorola Razr 40 , like many other Android manufacturers, implements Factory Reset Protection. It acts as a preemptive safeguard against unauthorized access to a device after a reset. If your phone is linked to a Google account, you will need to input the accurate login credentials after a reset.
Failing to do so may lead to your device being locked. Understanding how to bypass or recover from FRP lock is essential if you find yourself in this situation.
Part 2: How to Reset a Motorola Razr 40 Phone That is Locked With Google Find My Device?
Resetting a locked Motorola Razr 40 phone through Google Find My Device presents a convenient solution. It, however, needs you to have activated this functionality on your device. To initiate the reset, please adhere to the following steps:
Step 1: Open a web browser on any computer or alternative device and navigate to the Google Find My Device website. Sign in with the same Google account associated with your locked Motorola Razr 40 phone.
Step 2: Upon successful login, a list of devices linked to your Google account will be displayed. Locate your locked Motorola Razr 40 phone from the list and select it. Select the “Erase Device” option from the left-hand panel, and it will trigger a remote factory reset for your locked phone.
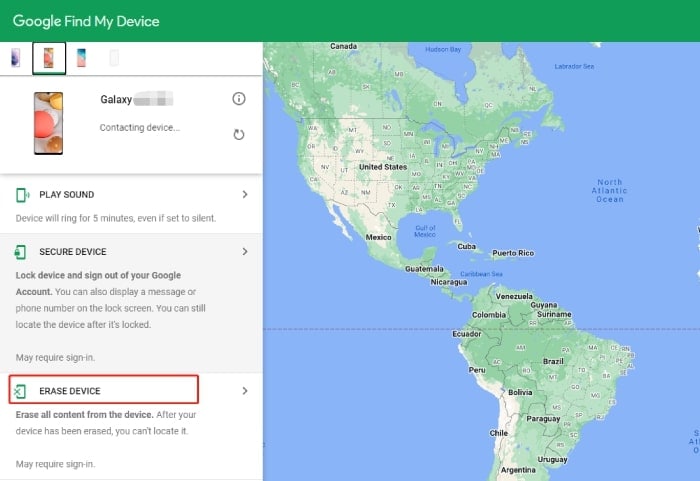
Step 3: A confirmation dialog will appear, prompting you to input your Google account password. Finally, click the “Erase” button to initiate the factory reset process.
Part 3: How to reset a Motorola Razr 40 phone that is locked without a password?
In order to reset your Motorola Razr 40 phone without a password, you need to have a single software known as Dr.Fone - Screen Unlock (Android) . It’s a powerful and versatile software tool designed to help you unlock your devices under various circumstances. Whether you’ve forgotten your device’s password, PIN, pattern, or fingerprint, or you’re dealing with a locked device due to a broken screen, Dr.Fone - Screen Unlock (Android) can assist you. In order to reset phone correctly, go through the steps given below:
Before resetting your Motorola Razr 40 phone that is locked, you can install the Dr.Fone application on your Windows PC or Mac first.

Dr.Fone - Screen Unlock (Android)
The Best Unlock Tool to Reset a Motorola Razr 40 Phone That Is Locked Without a Password!
- Remove all Android screen locks (PIN/pattern/fingerprints/face ID) in minutes.
- Work for forgotten passwords, second-hand Motorola Razr 40 devices, etc.
- Everyone can handle the lock screen without any tech knowledge.
- Provide specific removal solutions to promise good success rate.
4,008,671 people have downloaded it
Step 1: Launch the Program
First of all, launch the Dr.Fone Screen Unlock on your computer, and you will be greeted with a welcome screen like this. Now, head over to the “Screen Unlock” section.
Step 2: Connect Device
Now, you need to connect your Motorola Razr 40 phone to the computer via a USB cable and select “Android” > “Unlock Android Screen.” This particular step is an application for all the Android phones out there.
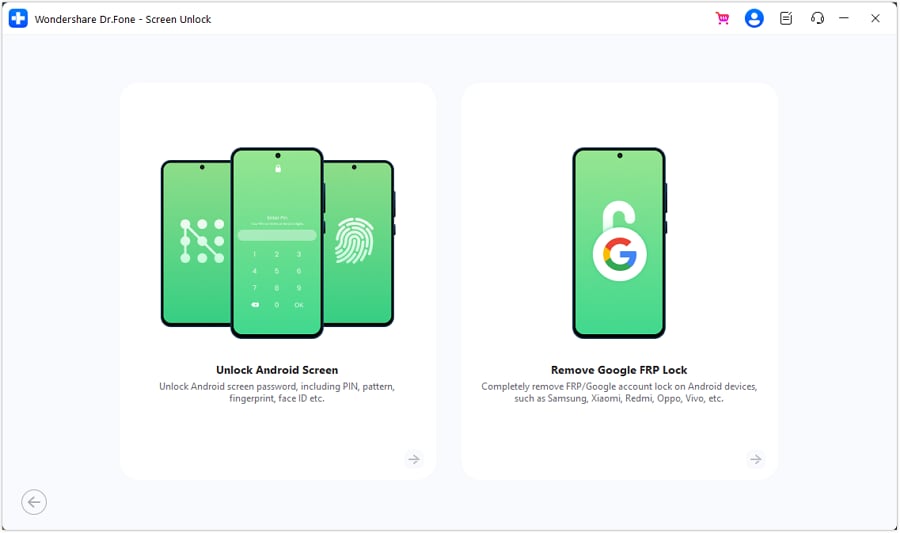
Step 3: Choose Device Model
Here you need to select the exact brand of your phone. In your case, you can just tap “Motorola Razr 40 .” The program then will start the process for the lock screen removal.
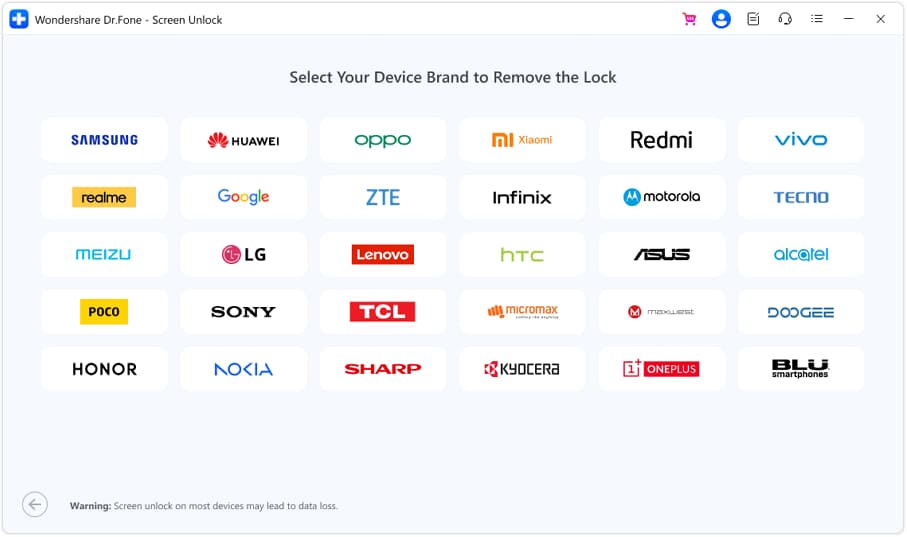
Step 4: Unlock Screen
Go along with the instructions on the screen and remove all the settings of the Motorola Razr 40 device. Within a short while, the screen will be unlocked.
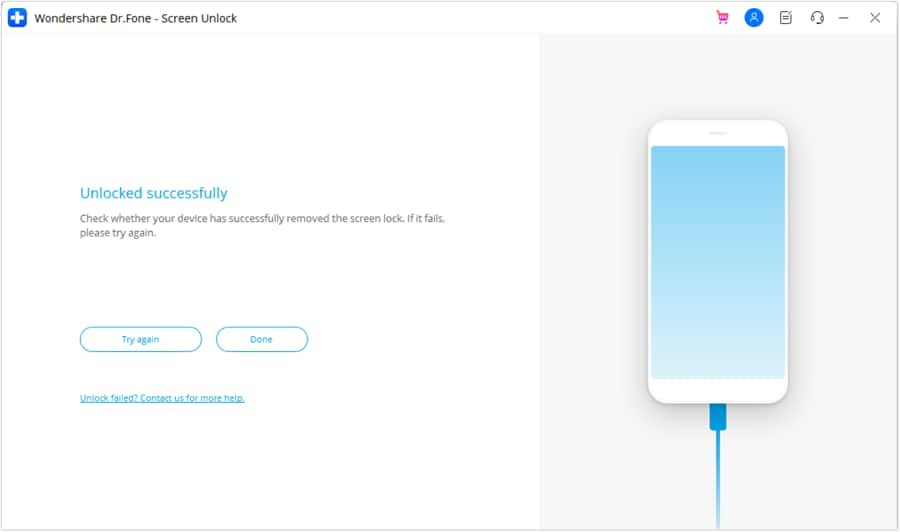
After the entire process is completed, you can easily access your Motorola Razr 40 Phone without the need to enter your password. All the restrictions that were set properly to unlock will be removed so that you can use your phone as intended.
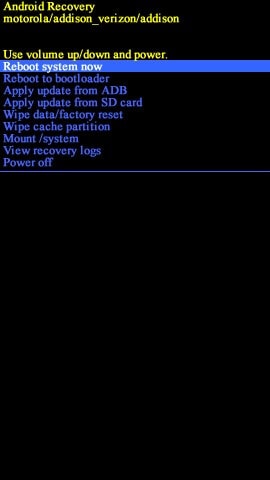
Part 4: How to reset a Motorola Razr 40 phone that is locked with a hard reset
Disclaimer: Only perform this step if you are well accustomed to the Android recovery system or at least know your way around your Motorola Razr 40 phone.
That being said, you should only resort to using a hard reset if you don’t have any important data on your phone. Further including, resetting your phone with the hard reset option will wipe out any data that’s been stored in it. Now, proceed forward will all the steps are given below:
Step 1: Charge Device
Charge your Motorola Razr 40 Phone so that it has a batter of at least 30% or higher. Then turn off the phone.
Step 2: Press keys
Now, you need to press the Volume Down + Power button simultaneously until the Motorola Razr 40 device logo shows up on the screen.
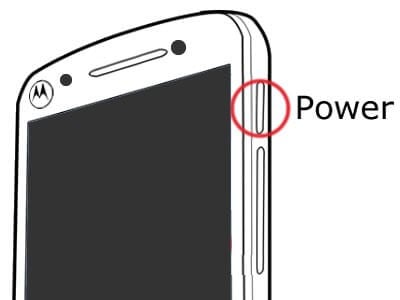
Step 3: Enter Recovery Mode
Now, press the Volume Down button to navigate to the Recovery Mode.
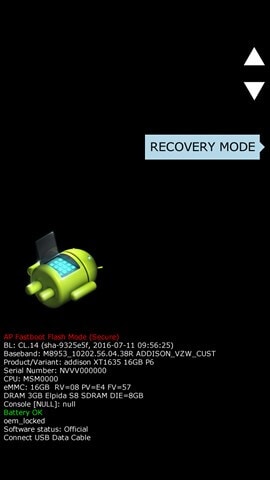
Step 4: Factory Reset
Use the buttons to navigate to the “Wipe data/factory reset” option and select it by pressing the Power button. Now, choose the option ”Factory data Reset” and wait for a few seconds till it is completed.
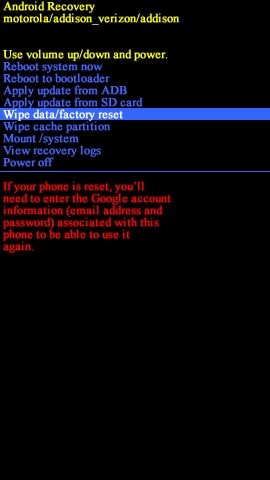
Step 5: Reboot Now
Again use the Volume buttons and select the “Reboot system now.”
After you have successfully reset your Motorola Razr 40 phone, it would take a few minutes to boot up. Once that is done, you are left with a clean slate, just like a completely new smartphone.
Part 5: Unlock locked Motorola Razr 40 phone with Gmail ID and password
It is imperative to understand that unlocking your Motorola Razr 40 Phone using a Gmail ID and password should be your last resort and especially if you are using an older version of Android. Among all the tricks of how to reset a Motorola Razr 40 phone that is locked, it only works if you are running around version 4.4 KitKat or older than that. Neither less to say, in order for the step to work properly, you need your Gmail account to be properly configured with the Motorola Razr 40 device.
Step 1: Attempt Passwords
At first, you need to make five attempts to unlock your device. Whether you have used a PIN or Pattern lock, Android will always give you five attempts to get the password right. Once you get that, it will trigger the “Forget Password/Pattern” option on Your Motorola Razr 40. This way, you can sneak back into the system once again.

Step 2: Enter Credentials
Once you hit the option, you will be redirected to another page, where you need to enter your Gmail id and password. Make sure that you get the information right, and select “Sign in.”

Once you get everything right, this will bypass any password or pattern you once had put on your Phone. Just remember, you need to have a stable internet connection in order for the step to work seamlessly.
Bonus Tip: Are There Preventive Measures To Avoid Future Lockouts?
Want to prevent future lockouts and ensure a smoother smartphone experience? Consider implementing the following preventive measures:
1. Setting Up Alternative Lock Methods
One way to avoid getting locked out of your Motorola Razr 40 phone is to set up alternative lock methods. In addition to PINs, passwords, and patterns, you can use biometric methods. These include fingerprint recognition or facial recognition if your device supports them. Such options provide convenient and secure ways to unlock your phone.
2. Regularly Backing Up Your Data
Regular data backups are crucial to safeguarding your essential files and information. Utilize cloud backup services or local backup solutions to routinely save your data. In case of a lockout or a factory reset, you can quickly restore your data without loss.
3. Using Secure and Memorable Passwords
When setting up lock methods, opt for strong, unique, and memorable passwords. Avoid using easily guessable information like birthdays or simple patterns. Strong passwords can enhance security while minimizing the chances of forgetting your credentials.
Conclusion
There is no point in arguing that looking through how to reset a Motorola Razr 40 phone that is locked after you have forgotten the password is indeed a hectic process. But, there is a way around it too. By going through all the steps mentioned above, you can always get an unlocked phone with ease.
To our recommendation, we would suggest going through Dr.Fone - Screen Unlock (Android) so that you can make the entire process as seamless as possible. It is by far the easiest and most convenient process to work around. Neither less to say, there are a ton of video tutorials that can assist you in case you get stuck in the middle of the process.
Top 10 Password Cracking Tools For Motorola Razr 40
What is password cracking?
Password cracking process involves recovering a password from storage locations or from data, transmitted by a computer system on network. Password cracking term refers to group of techniques used to get password from a data system.
Purpose and reason of password cracking includes gaining an unauthorized access to a computer system or it can be recovery of forgotten password. There might be another reason of using password cracking technique that is for testing password strength so hacker could not hack into system.
Password cracking is normally performed thought repetitive process in which computer applies different combinations of password till the exact match.
Brute Force Password Cracking:
Term brute force password cracking may also be referred as brute force attack. Brute force password cracking is respective process of guessing password, in this process software or tool creates a large number of password combinations. Basically it’s a trail-and-error technique used by software to obtain password information from system.
A brute force attack are normally used by hackers when there is no chance of taking advantage of encrypted system weakness or by security analysis experts to test an organization’s network security .This method of password cracking is very fast for short length passwords but for long length passwords dictionary attack technique is normally used.
Time taken by brute force password cracking software to crack password is normally depend upon speed of system and internet connection.
GPU Password Cracking:
GPU is graphics processing unit, sometimes also called visual processing unit. Before talking about GPU password cracking we must have some understanding about hashes . When user enter password the password information stored in form of computer hashes using the one-way hashing algorithm.
In this password cracking technique using GPU software take a password guess and look through hashing algorithm and compare it or match it with the existing hashes till the exact match.
GPU can perform mathematical functions in parallel as GPU have hundreds of core that gives massive advantage in cracking password. GPU is much faster than CPU so that’s the reason of using GPU instead of CPU.
CUDA Password Cracking:
CUDA Compute Unified Device Architecture is a model for programming and a platform that perform computations in parallel, created by NVIDIA for graphic processing.
CUDA Password cracking includes cracking passwords using Graphics card which have GPU chip, GPU can perform mathematical functions in parallel so the speed of cracking password is faster than CPU.GPU have many 32bit chips on it that perform this operation very quickly.
We can easily access CUDA through libraries, directives and with the help of different programming languages that includes C, C++ and FORTRAN.
Password Cracking Tools
Given below is the list of Top10 Password cracking tools.
1. Cain and Abel : Top password cracking tool for Windows
Cain & Abel is one of the top cracking tool for password cracking and password recovery for Windows OS.
Cain & Abel can use techniques of Dictionary Attack, Brute-Force and Cryptanalysis attacks to crack encrypted passwords. So it only uses the weakness of system to crack password. GUI Interface of software is very simple and easy to use. But have availability limitation, tool only available for window based systems .Cain & Abel tool have many good features some of the features of tool are discussed below:
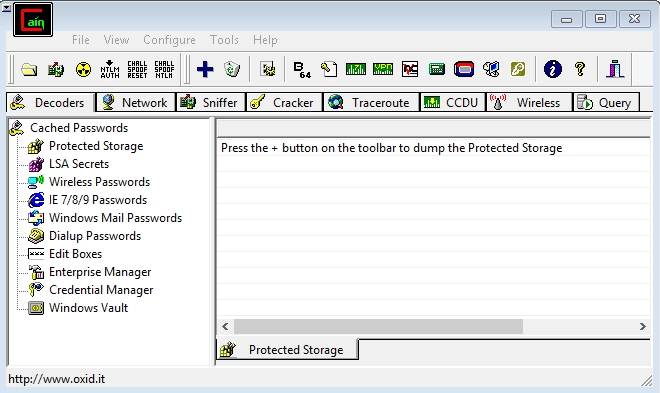
Features of Cain & Abel:
- Used for WEP (Wired Equivalent Privacy) cracking
- Have ability to record conversation over IP
- Cab be used as Network Password Sniffer
- Ability to resolve addresses IP to MAC.
- Can crack verity of hashes including LM and NT hashes, IOS and PIX hashes, RADIUS hashes, RDP passwords, and lots more than that.
Site for Download:
2. John the Ripper : Multi-platform, Powerful, Flexible password cracking tool
John the Ripper is a free multi or cross platform password cracking software. Its called multi platform as it combines different password cracking features into one package.
It’s primarily used to crack weak UNIX passwords but also available for Linux, Mac, and Windows. We can run this software against different password encryptions including many password hashes normally found in different UNIX versions. These hashes are DES, LM hash of Windows NT/2000/XP/2003, MD5, and AFS.
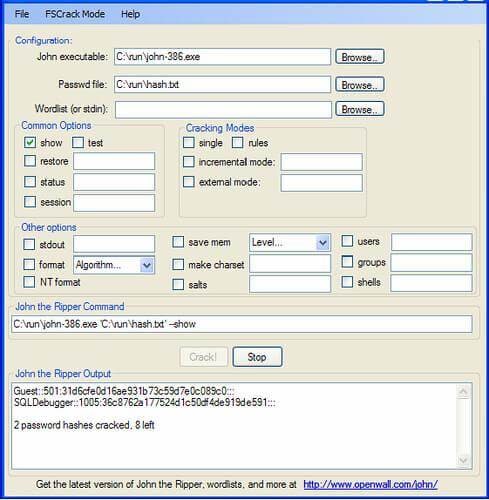
Features of John the Ripper
- Supportive with Brute force password cracking and dictionary attacks
- Multi platform
- Available free for use
- Pro version is also available with additional features
Site for Download:
3. Aircrack : Fast and effective WEP/WPA cracking tool
Aircrack is a combination different tools used for Wifi, WEP and WPA passwords cracking. With the help of these tools you can crack WEP/WPA passwords easily and effectively
Brute force, FMS attack, and dictionary attacks techniques can be used to crack WEP/WPA passwords. Basically it collects and analyzes encrypted packets then using its different tool crack password out of the packets. Although aircrack is available for Windows but there are different issues with this software if we use this in Windows environment, so it’s best when we use it in Linux environment.
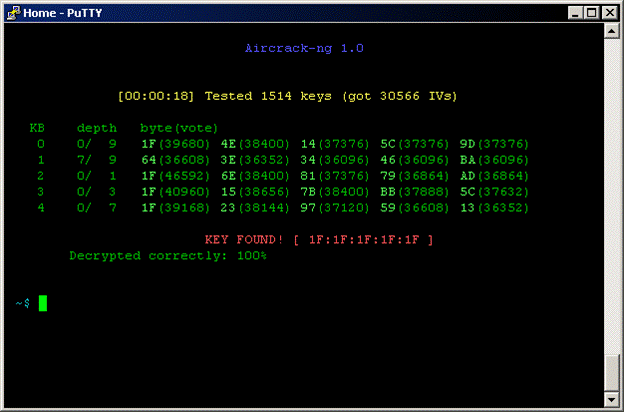
Features of Aircrack
- Supportive with both Brute force and dictionary attacks cracking techniques
- Available for Windows and Linux
- Available in live CD
Site for Download:
4. THC Hydra : Multiple services supportive, Network authentication cracker
THC Hydra is a supper fast network password cracking tool. It uses network to crack remote systems passwords.
It can be used to crack passwords of different protocols including HTTPS, HTTP, FTP, SMTP, Cisco, CVS, SQL, SMTP etc. It will give you option that you may supply a dictionary file that contains list of possible passwords. It’s best when we use it in Linux environment.

Features of THC Hydra
- Fast cracking speed
- Available for Windows, Linux ,Solaris and OS X
- New modules can be added easily to enhance features
- Supportive with Brute force and dictionary attacks
Site for Download:
https://www.thc.org/thc-hydra/
5. RainbowCrack : New Innovation in Password Hash Cracker
RainbowCrack software uses rainbow tables to crack hashes, in other words we can say it uses process of a large-scale time-memory trade for effective and fast password cracking.
Large-scale-time-memory-trade-off is a process of computing all hashes and plain text using a selected hash algorithm. After calculations, obtained results are stored in the tables called rainbow table. Process of creating rainbow tables is very time consuming but when its done software works very fast.
Password cracking using rainbow table is faster than the normal brute force attack method. It’s available for Linux and Windows operating system.
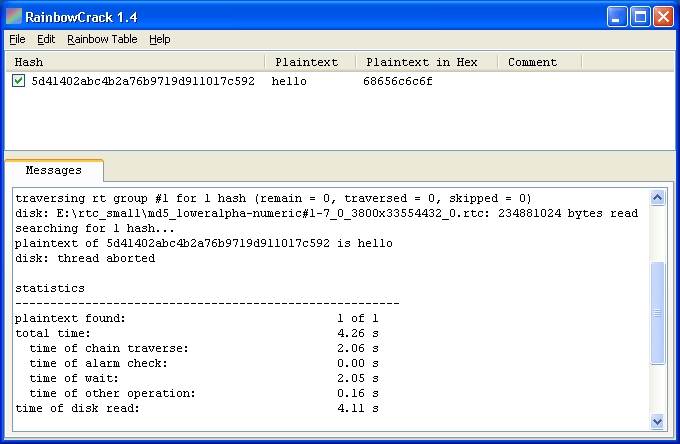
Features of Rainbow Crack
- Support verity of Rainbow tables
- Runs on Windows (XP/Vista/7/8) and Linux operating systems (x86 and x86_64)
- Simple in use
Site for Download:
http://project-rainbowcrack.com/
6. OphCrack : Tool for Windows password cracking
OphCrack used to crack Windows user passwords with the help of rainbow tables that are available in a bootable CD.
Ophcrack is completely free to download, Windows based password cracker that uses rainbow tables to crack Windows user passwords. It normally cracks LM and NTLM hashes. Software has simple GUI and can runs on different platforms.
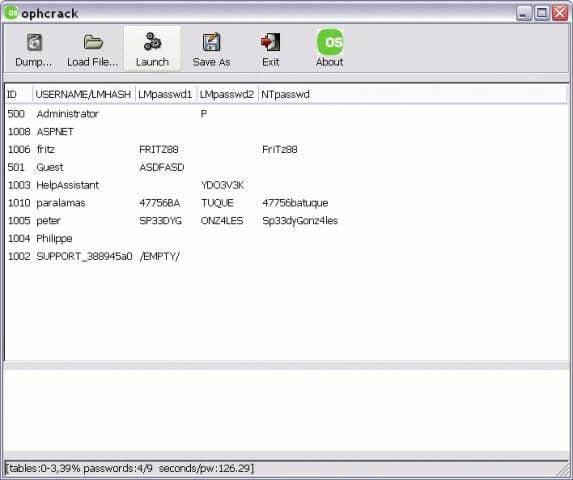
Features of OphCrack
- Available for Windows but also available for Linux, Mac, Unix, and OS X
- Uses for LM hashes of Windows and NTLM hashes of Windows vista.
- Rainbow tables available free and easily for Windows
- To simplify the process of cracking Live CD is available
Site for Download:
http://ophcrack.sourceforge.net/
7. Brutus : A brute force attack cracker for remote systems
Brutus is the fastest, most flexible, and most popular software used to crack remote system passwords. It guess password through applying different permutations or by using a dictionary.
It can be used for different network protocols including HTTP, FTP, IMAP, NNTP and other types such as SMB, Telnet etc. It also gives you facility of creating your own authentication type. It also includes extra options of load and resume, so process can be paused when required and you can resume process when you want.
It is only available for windows operation systems. Tool has a limitation that it has not been updated since 2000.

Features of Brutus
- Available for Windows
- Can be used with different network protocols
- Tool have many good extra features
- Support SOCK proxy for all types of authentications
- Capability of error handling and recovery
- Authentication engine is multi stage
Site for Download:
8. L0phtCrack : Smart tool for Windows password recovery
Just like OphCrack tool L0phtCrack is also a Windows passwords recovery tool uses hashes to crack passwords, with extra features of Brute force and dictionary attacks .
It normally gains access to these hashes from directories, network servers, or domain controllers. It is capable of doing hash extraction from 32 & 64 bit Windows systems, multiprocessor algorithms, scheduling, and can also perform decoding and monitoring networks. Yet it is still the easiest to use password auditing and recovery software available.
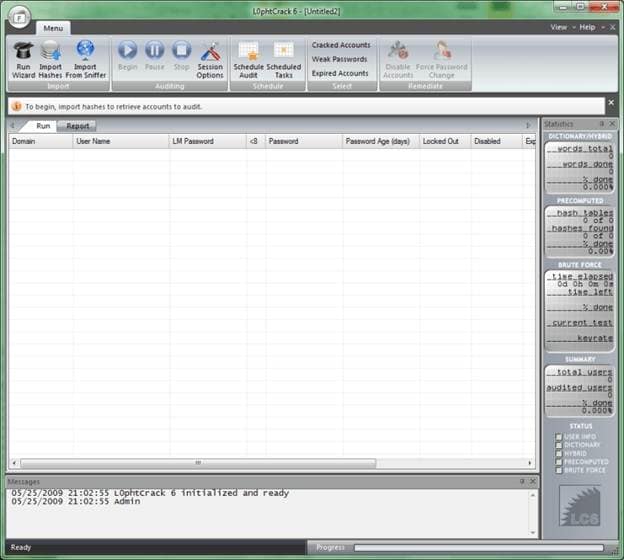
Features of L0phtCrack
- Available for Windows XP, NT, 2000, Server 2003,and Server 2008
- Can work in both 32- and 64-bit environments
- Extra feature of schedule routine auditing on daily, weekly, monthly bases
- After run it provide complete Audit Summary in report page
Site for Download:
9. Pwdump : Password recovery tool for Windows
Pwdump is actually different Windows programs that are used to provide LM and NTML hashes of system user accounts.
Pwdump password cracker is capable of extracting LM, NTLM and LanMan hashes from the target in Windows, in case if Syskey is disabled, software has the ability to extract in this condition.
Software is update with extra feature of password histories display if history is available. Extracted data will be available in form that is compatible with L0phtcrack.
Recently software is updated to new version called Fgdump as Pwdump not work fine when any antivirus program is running.
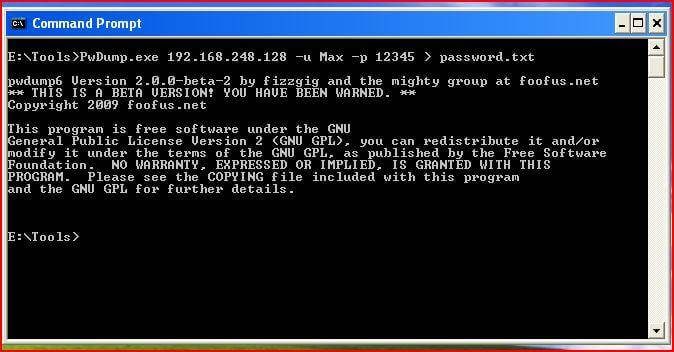
Features of Pwdump
- Available for Windows XP, 2000
- Powerful extra feature are available in new version of Pwdump
- Ability to run multithreaded
- It can perform cachedump (Crashed credentials dump) and pstgdump (Protected storage dump)
Site for Download:
10. Medusa : Speedy network password cracking tool
Medusa is remote systems password cracking tool just like THC Hydra but its stability, and fast login ability prefer him over THC Hydra.
It is speedy brute force, parallel and modular tool. Software can perform Brute force attack against multiple users, hosts, and passwords. It supports many protocols including AFP, HTTP, CVS, IMAP, FTP, SSH, SQL, POP3, Telnet and VNC etc.
Medusa is pthread-based tool, this feature prevent unnecessarily duplicate of information. All modules available as an independent .mod file, so no modification is required to extend the list that supports services for brute forcing attack.
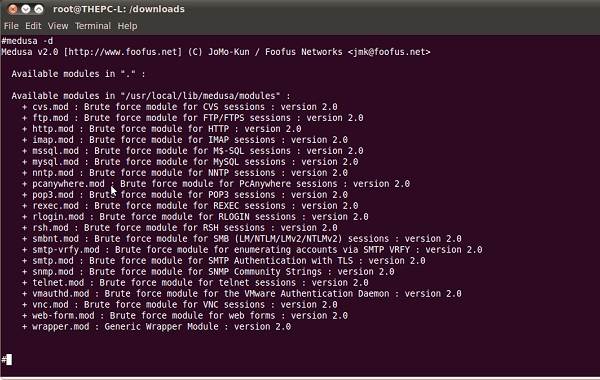
Features of Medusa
- Available for Windows, SunOS, BSD, and Mac OS X
- Capable of performing Thread based parallel testing
- Good feature of Flexible user input
- Due to parallel processing speed of cracking is very fast
Site for Download:
Also read:
- [New] 2024 Approved Quick Tips to Produce Quality Thumbnails Fast
- [New] Efficient Strategies for Large Scale TikTok Content Acquisition for 2024
- [Updated] Diving Deep Into Valheim's Vital Vegetation for 2024
- 2024 Approved Clash of Shadows and Lightning BLACK vs SILVER
- How to Unlock Motorola Moto G Stylus 5G (2023) Pattern Lock if Forgotten? 6 Ways
- In 2024, Full Tutorial to Bypass Your Motorola Moto G Stylus 5G (2023) Face Lock?
- In 2024, Radiant Reality Tiles Photographic Collages That Sparkle
- In 2024, Tips and Tricks for Setting Up your Asus ROG Phone 7 Phone Pattern Lock
- In 2024, Unlock Your Huawei Nova Y71s Potential The Top 20 Lock Screen Apps You Need to Try
- Introducing Noctua's Premium £99 Air Cooler: The Ultimate NH-D12L Chromax Black Model
- Lock Your Motorola Razr 40 Ultra Phone in Style The Top 5 Gesture Lock Screen Apps
- The Artist's Toolkit Creating Collages
- Ultimate Tutorial: Capturing and Saving BBC iPlayer TV Episodes for Later Viewing on a Computer
- Title: Top 4 SIM Location Trackers To Easily Find Your Lost Motorola Razr 40 Device
- Author: Peter
- Created at : 2024-10-17 16:24:21
- Updated at : 2024-10-19 19:14:32
- Link: https://android-unlock.techidaily.com/top-4-sim-location-trackers-to-easily-find-your-lost-motorola-razr-40-device-by-drfone-android/
- License: This work is licensed under CC BY-NC-SA 4.0.
