
In 2024, Top 10 Password Cracking Tools For Motorola Edge 40 Pro

Top 10 Password Cracking Tools For Motorola Edge 40 Pro
What is password cracking?
Password cracking process involves recovering a password from storage locations or from data, transmitted by a computer system on network. Password cracking term refers to group of techniques used to get password from a data system.
Purpose and reason of password cracking includes gaining an unauthorized access to a computer system or it can be recovery of forgotten password. There might be another reason of using password cracking technique that is for testing password strength so hacker could not hack into system.
Password cracking is normally performed thought repetitive process in which computer applies different combinations of password till the exact match.
Brute Force Password Cracking:
Term brute force password cracking may also be referred as brute force attack. Brute force password cracking is respective process of guessing password, in this process software or tool creates a large number of password combinations. Basically it’s a trail-and-error technique used by software to obtain password information from system.
A brute force attack are normally used by hackers when there is no chance of taking advantage of encrypted system weakness or by security analysis experts to test an organization’s network security .This method of password cracking is very fast for short length passwords but for long length passwords dictionary attack technique is normally used.
Time taken by brute force password cracking software to crack password is normally depend upon speed of system and internet connection.
GPU Password Cracking:
GPU is graphics processing unit, sometimes also called visual processing unit. Before talking about GPU password cracking we must have some understanding about hashes . When user enter password the password information stored in form of computer hashes using the one-way hashing algorithm.
In this password cracking technique using GPU software take a password guess and look through hashing algorithm and compare it or match it with the existing hashes till the exact match.
GPU can perform mathematical functions in parallel as GPU have hundreds of core that gives massive advantage in cracking password. GPU is much faster than CPU so that’s the reason of using GPU instead of CPU.
CUDA Password Cracking:
CUDA Compute Unified Device Architecture is a model for programming and a platform that perform computations in parallel, created by NVIDIA for graphic processing.
CUDA Password cracking includes cracking passwords using Graphics card which have GPU chip, GPU can perform mathematical functions in parallel so the speed of cracking password is faster than CPU.GPU have many 32bit chips on it that perform this operation very quickly.
We can easily access CUDA through libraries, directives and with the help of different programming languages that includes C, C++ and FORTRAN.
Password Cracking Tools
Given below is the list of Top10 Password cracking tools.
1. Cain and Abel : Top password cracking tool for Windows
Cain & Abel is one of the top cracking tool for password cracking and password recovery for Windows OS.
Cain & Abel can use techniques of Dictionary Attack, Brute-Force and Cryptanalysis attacks to crack encrypted passwords. So it only uses the weakness of system to crack password. GUI Interface of software is very simple and easy to use. But have availability limitation, tool only available for window based systems .Cain & Abel tool have many good features some of the features of tool are discussed below:
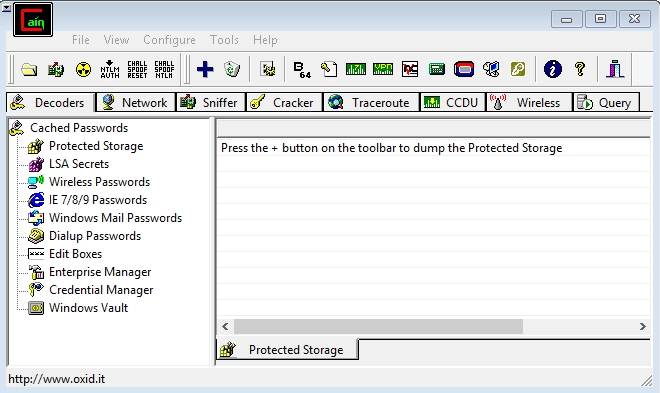
Features of Cain & Abel:
- Used for WEP (Wired Equivalent Privacy) cracking
- Have ability to record conversation over IP
- Cab be used as Network Password Sniffer
- Ability to resolve addresses IP to MAC.
- Can crack verity of hashes including LM and NT hashes, IOS and PIX hashes, RADIUS hashes, RDP passwords, and lots more than that.
Site for Download:
2. John the Ripper : Multi-platform, Powerful, Flexible password cracking tool
John the Ripper is a free multi or cross platform password cracking software. Its called multi platform as it combines different password cracking features into one package.
It’s primarily used to crack weak UNIX passwords but also available for Linux, Mac, and Windows. We can run this software against different password encryptions including many password hashes normally found in different UNIX versions. These hashes are DES, LM hash of Windows NT/2000/XP/2003, MD5, and AFS.
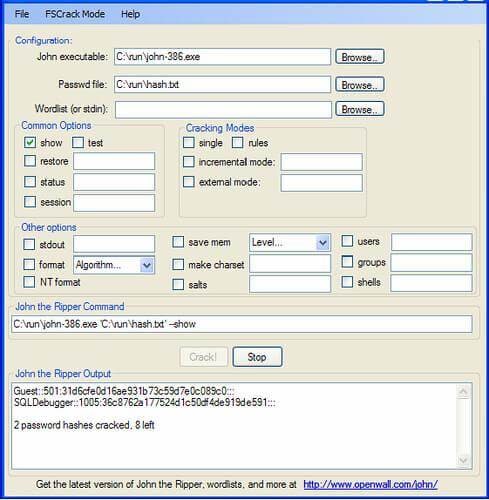
Features of John the Ripper
- Supportive with Brute force password cracking and dictionary attacks
- Multi platform
- Available free for use
- Pro version is also available with additional features
Site for Download:
3. Aircrack : Fast and effective WEP/WPA cracking tool
Aircrack is a combination different tools used for Wifi, WEP and WPA passwords cracking. With the help of these tools you can crack WEP/WPA passwords easily and effectively
Brute force, FMS attack, and dictionary attacks techniques can be used to crack WEP/WPA passwords. Basically it collects and analyzes encrypted packets then using its different tool crack password out of the packets. Although aircrack is available for Windows but there are different issues with this software if we use this in Windows environment, so it’s best when we use it in Linux environment.
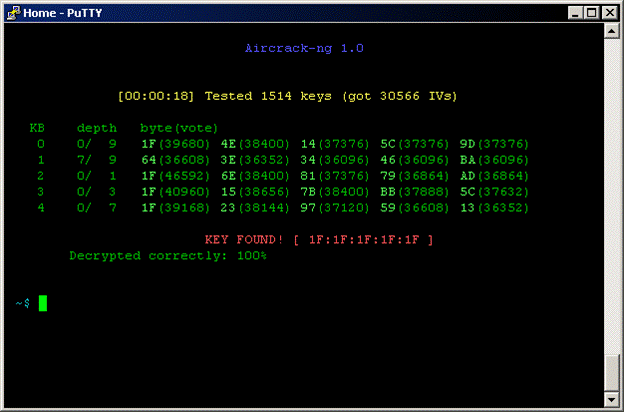
Features of Aircrack
- Supportive with both Brute force and dictionary attacks cracking techniques
- Available for Windows and Linux
- Available in live CD
Site for Download:
4. THC Hydra : Multiple services supportive, Network authentication cracker
THC Hydra is a supper fast network password cracking tool. It uses network to crack remote systems passwords.
It can be used to crack passwords of different protocols including HTTPS, HTTP, FTP, SMTP, Cisco, CVS, SQL, SMTP etc. It will give you option that you may supply a dictionary file that contains list of possible passwords. It’s best when we use it in Linux environment.

Features of THC Hydra
- Fast cracking speed
- Available for Windows, Linux ,Solaris and OS X
- New modules can be added easily to enhance features
- Supportive with Brute force and dictionary attacks
Site for Download:
https://www.thc.org/thc-hydra/
5. RainbowCrack : New Innovation in Password Hash Cracker
RainbowCrack software uses rainbow tables to crack hashes, in other words we can say it uses process of a large-scale time-memory trade for effective and fast password cracking.
Large-scale-time-memory-trade-off is a process of computing all hashes and plain text using a selected hash algorithm. After calculations, obtained results are stored in the tables called rainbow table. Process of creating rainbow tables is very time consuming but when its done software works very fast.
Password cracking using rainbow table is faster than the normal brute force attack method. It’s available for Linux and Windows operating system.
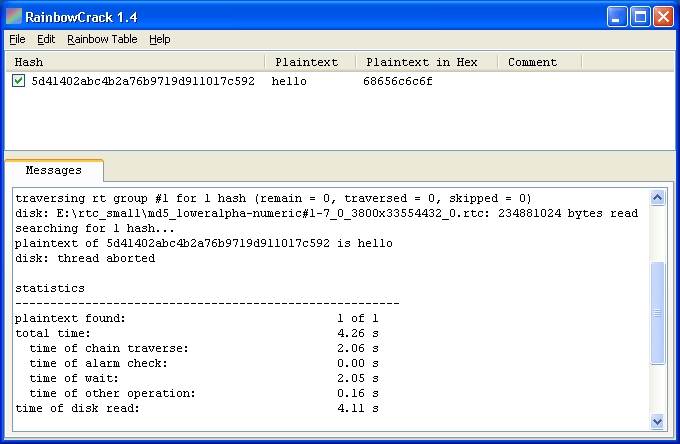
Features of Rainbow Crack
- Support verity of Rainbow tables
- Runs on Windows (XP/Vista/7/8) and Linux operating systems (x86 and x86_64)
- Simple in use
Site for Download:
http://project-rainbowcrack.com/
6. OphCrack : Tool for Windows password cracking
OphCrack used to crack Windows user passwords with the help of rainbow tables that are available in a bootable CD.
Ophcrack is completely free to download, Windows based password cracker that uses rainbow tables to crack Windows user passwords. It normally cracks LM and NTLM hashes. Software has simple GUI and can runs on different platforms.
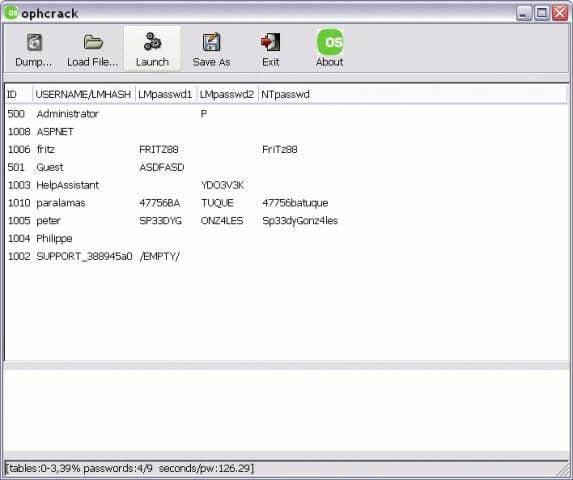
Features of OphCrack
- Available for Windows but also available for Linux, Mac, Unix, and OS X
- Uses for LM hashes of Windows and NTLM hashes of Windows vista.
- Rainbow tables available free and easily for Windows
- To simplify the process of cracking Live CD is available
Site for Download:
http://ophcrack.sourceforge.net/
7. Brutus : A brute force attack cracker for remote systems
Brutus is the fastest, most flexible, and most popular software used to crack remote system passwords. It guess password through applying different permutations or by using a dictionary.
It can be used for different network protocols including HTTP, FTP, IMAP, NNTP and other types such as SMB, Telnet etc. It also gives you facility of creating your own authentication type. It also includes extra options of load and resume, so process can be paused when required and you can resume process when you want.
It is only available for windows operation systems. Tool has a limitation that it has not been updated since 2000.

Features of Brutus
- Available for Windows
- Can be used with different network protocols
- Tool have many good extra features
- Support SOCK proxy for all types of authentications
- Capability of error handling and recovery
- Authentication engine is multi stage
Site for Download:
8. L0phtCrack : Smart tool for Windows password recovery
Just like OphCrack tool L0phtCrack is also a Windows passwords recovery tool uses hashes to crack passwords, with extra features of Brute force and dictionary attacks .
It normally gains access to these hashes from directories, network servers, or domain controllers. It is capable of doing hash extraction from 32 & 64 bit Windows systems, multiprocessor algorithms, scheduling, and can also perform decoding and monitoring networks. Yet it is still the easiest to use password auditing and recovery software available.
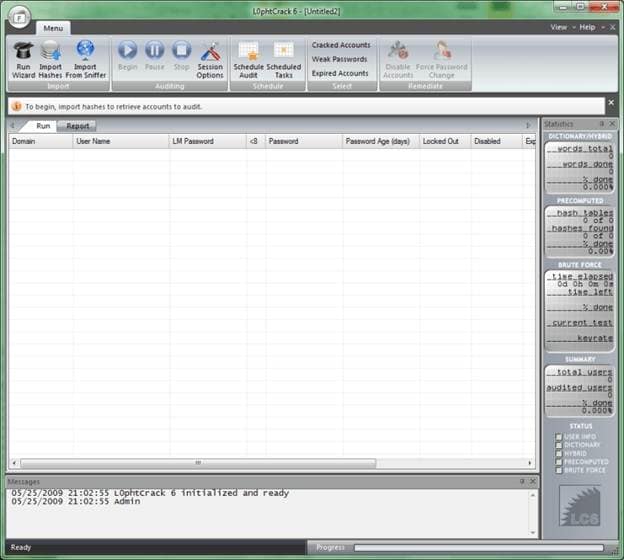
Features of L0phtCrack
- Available for Windows XP, NT, 2000, Server 2003,and Server 2008
- Can work in both 32- and 64-bit environments
- Extra feature of schedule routine auditing on daily, weekly, monthly bases
- After run it provide complete Audit Summary in report page
Site for Download:
9. Pwdump : Password recovery tool for Windows
Pwdump is actually different Windows programs that are used to provide LM and NTML hashes of system user accounts.
Pwdump password cracker is capable of extracting LM, NTLM and LanMan hashes from the target in Windows, in case if Syskey is disabled, software has the ability to extract in this condition.
Software is update with extra feature of password histories display if history is available. Extracted data will be available in form that is compatible with L0phtcrack.
Recently software is updated to new version called Fgdump as Pwdump not work fine when any antivirus program is running.
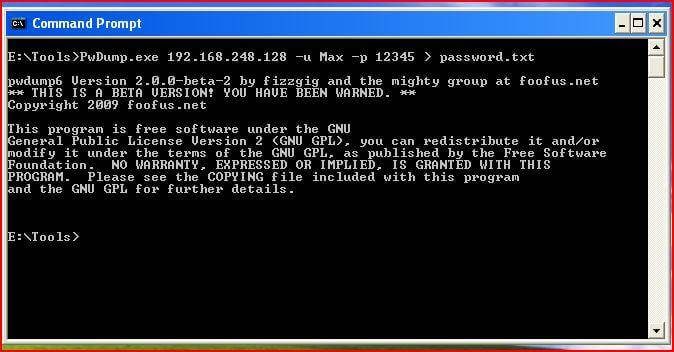
Features of Pwdump
- Available for Windows XP, 2000
- Powerful extra feature are available in new version of Pwdump
- Ability to run multithreaded
- It can perform cachedump (Crashed credentials dump) and pstgdump (Protected storage dump)
Site for Download:
10. Medusa : Speedy network password cracking tool
Medusa is remote systems password cracking tool just like THC Hydra but its stability, and fast login ability prefer him over THC Hydra.
It is speedy brute force, parallel and modular tool. Software can perform Brute force attack against multiple users, hosts, and passwords. It supports many protocols including AFP, HTTP, CVS, IMAP, FTP, SSH, SQL, POP3, Telnet and VNC etc.
Medusa is pthread-based tool, this feature prevent unnecessarily duplicate of information. All modules available as an independent .mod file, so no modification is required to extend the list that supports services for brute forcing attack.
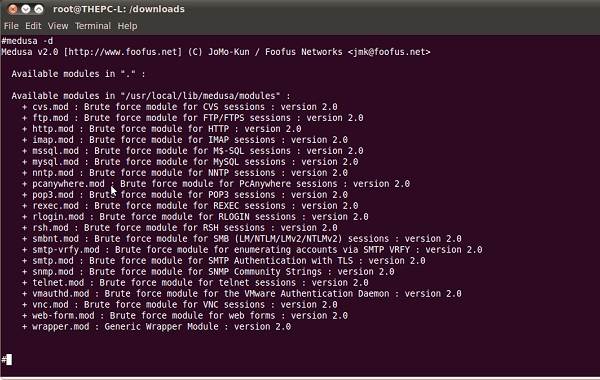
Features of Medusa
- Available for Windows, SunOS, BSD, and Mac OS X
- Capable of performing Thread based parallel testing
- Good feature of Flexible user input
- Due to parallel processing speed of cracking is very fast
Site for Download:
How To Easily Unlock Motorola Screen?
If you’ve ever had a Motorola phone, then you know that their screens are locked by default. It can be a pain if you want to access your messages or change your background image quickly. If you just set your Motorola password, screen lock code, pattern lock, or PIN last night or a few days ago, you are most likely to forget it.
The result is that you have locked out of your phone, and you have to reset your device’s password. But fortunately, there’s an easy way to unlock your Motorola screen without entering any passwords. You can have your phone up and running in a few simple steps without contacting customer service.
So don’t wait any longer - read on for instructions on how to unlock the Motorola phone pin code.
Let’s get started!
4 Easy Ways To Unlock Motorola Screen
Like most people, you probably lock your Motorola phone as soon as you turn it on. It’s a good way to keep your phone safe from prying eyes and accidental button presses. But what happens when you forget your phone’s passcode? Or worse, what if your phone gets locked by a malicious app?
There are a few different ways to unlock your Motorola phone. We’ll show you how to do it.
Method 1. Google Find My Device (Without Password/Pin/Pattern)
If you’re like me, you’ve probably tried a million different ways to unlock your Motorola phone, only to be frustrated by the results. Luckily, there’s an easy way to unlock your Motorola phone using Google’s Find My Device feature.
Google will use your location, phone information, and connection log to find your Nokia.
Follow these steps to unlock the Motorola lock screen password without losing data:
- Step 1: Sign into your Google account and navigate the Find My Device website.

- Step 2: Sign in with your Google account, which you used on your locked Motorola phone.
- Step 3: The Android Device Manager dashboard will show your locked Motorola with three options: Ring, Lock, and Erase.
- Step 4: Simply click on “Lock”.
- Step 5: Enter a password that is not your Google account password in the “New Password” field.
- Step 6: Type the new password in the “Confirm password” field. This password lock will replace the current lock screen.
- Step 7: You can leave the “Recovery message” field empty or type anything in it.
- Step 8: Enter another phone number in the “Phone number” field, although this is optional.
- Step 9: Choose “Lock” after entering your password and filling out the optional fields if you wish.
- Step 10: If the process is successful, you will receive the unlock code within a few seconds.
- Step 11: Navigate to the “Screen Settings” menu after unlocking your device.
- Step 12: Use a new password; you can use the temporary password if you want.
You can use it to unlock your Motorola if you have activated the Android Device Manager or Google Find My Device before your phone was locked.
A few conditions, however, must be met for this to work
- You must turn on your Motorola phone.
- Before locking your phone, you must activate Google Find My Device or Android Device Manager.
- You must have your Motorola GPS turned on to use it.
- You must be connected to WiFi on your device to log into your Google account.
- Your phone needs to be set to location.
Method 2. Unlock Motorola Lock Screen With Hard Reset
If you perform a hard reset on your Motorola lock screen, all data, and user information will be erased, including your screen lock, password, pattern lock, and PIN.
Follow the steps below if you want to know how to unlock the Motorola phone keypad with the hard reset, follow the steps below.
- Step 1: Turn off your Motorola phone.
- Step 2: Press the “Volume down” and “Power key” buttons simultaneously for a few seconds.
- Step 3: Press the “Volume Up” and “Power” buttons for a few additional seconds once the screen darkens.
- Step 4: Release all buttons and keys if you did step 3 correctly. Once you release all buttons, you’ll see a dark screen with options.
- Step 5: Choose “Wipe data/factory reset” from the menu, using “Volume Up” to scroll up, “Volume Down” to scroll down, and “Power” to select.
- Step 6: From the Android Recovery screen, select the “Yes” option by pressing the “Volume Down” button and the “Power” key.
- Step 7: With the “Power” key, select “Reboot system now” from the next display.
Your Motorola is now password, pattern lock, screen lock, and PIN-free after a hard reset.
Method 3. Unlock With Answer Security Questions
You can reset the Motorola pattern lock using Google security questions without losing data.
Follow the steps below on how to unlock the Motorola phone pin code:
- Step 1: Power on your Nokia.
- Step 2: Press “Forgot pattern” several times until you see “Forgot password”.
- Step 3: Click on “Forgot pattern” to access the unlock screen.
- Step 4: Enter your Google account details or answer questions to unlock the screen. Select “Answer question”.
- Step 5: Enter your exact security answers and tap the “Unlock” button.
- Step 6: Choose “YES” from the “YES” or “NO” menu, and the password field will appear.
- Step 7: Change your password or PIN.
- Step 8: You will see your Motorola unlocked soon.
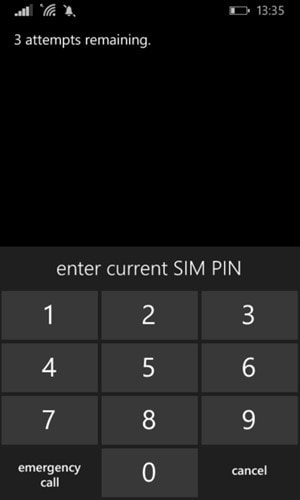
Method 4. Unlock the Keypad With a Security Code
You could reset your Motorola lock screen phone using the default security code, even if you haven’t set any security code. Here’s how to quickly unlock the Motorola lock screen security code.
- Step 1: Shut down your device.
- Step 2: Press these buttons in the following sequence on a classic phone.
Call button (green button) + Asterisk key (*) + Three (3)
- Step 3: Your screen displays a Formatting message when you press these keys.
- Step 4: Wait for the formatting to complete before releasing the keys.
o 12345.
Conclusion
If you have a classic-style keypad phone or an Android device, unlocking a locked Motorola phone keypad is not easy. However, we believe that every problem has a solution. You can unlock Motorola Android phones using any of the methods listed above.
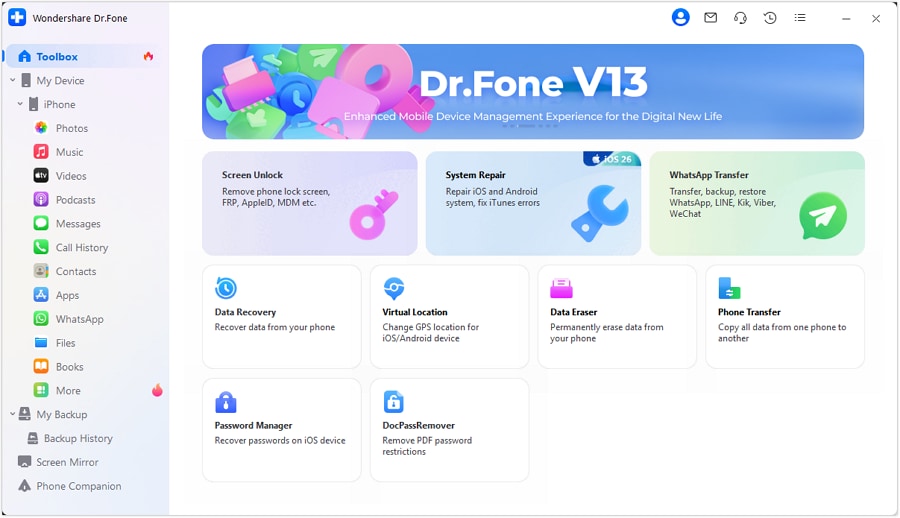
Tips: Wondershare Dr.Fone is a tool that helps you keep your important data safe. It can back up all the important information on your Motorola phone, like photos, music, videos, contacts, and more and is compatible with over 8000 Android devices. The backup process is easy and only takes a few clicks. You can also restore your backup to any device you want, and choose which data you want to restore. This is a great way to make sure you never lose your important Motorola data!
How To Remove or Bypass Knox Enrollment Service On Motorola Edge 40 Pro
In today’s digitally-driven work environment, many companies rely on Knox Enrollment Service to secure their employees’ phones and safeguard sensitive data. However, you might have a Knox-enrolled phone you wish to unlock for personal use.
This article will guide you through removing or bypassing the serviceon your phone. However, it’s important to note that this should ideally be done with your employer’s consent. For transitioning to personal use or other reasons, understanding how to remove or bypass Knox Enrollment Service can be crucial for some users.
Part 1: What Is the Knox Enrollment Service?
Knox Enrollment Service is an integral part of Samsung’s Knox, a toolbox of security features for enterprise-level management of mobile devices. This service is pivotal in how companies manage and secure their mobile devices, especially in a corporate environment.
What It Is
Knox Enrollment Service by Samsung is a tool businesses use to automatically enroll Samsung devices into their management systems when the Motorola Edge 40 Pro device is connected to the internet. It’s designed for IT administrators to easily deploy, manage, and enforce policies across devices in their network, ensuring consistency and security.
What It Does
The service allows IT administrators to pre-configure settings and apps and manage other aspects of the Motorola Edge 40 Pro device’s functionality. When a device is enrolled, it can be remotely controlled and monitored. The administrators can push updates, track device locations, remotely wipe data for security, and enforce specific compliance policies. This automation of device enrollment simplifies the setup process for both the IT department and the end-user.
Advantages
Of course, Samsung Knox would not be popular without any advantages. Here are some of them:
- Enhanced security. Knox Enrollment Service ensures corporate devices have robust security features. This helps in safeguarding sensitive data against unauthorized access.
- **Streamlined management.**It simplifies the Motorola Edge 40 Pro device management, allowing administrators to configure devices without physical access.
- The service enables the customization of devices to fit specific business needs, including installing necessary applications and restrictions on unauthorized apps.
- Compliance Assurance. With the ability to have policies remotely, companies can ensure that all devices comply with corporate standards and regulations.
Disadvantages
However, it also has some disadvantages:
- **Restrictive for users.**For employees, this can mean reduced control over their devices. After all, certain functionalities might be restricted by the employer.
- Potential privacy concerns. The ability of IT administrators to monitor and control devices may raise privacy concerns among employees.
- Complexity in management. While it simplifies many aspects, managing many devices through Knox can become complex. This is particular in diverse environments with different user needs.
Knox Enrollment Service is a powerful tool for enterprise mobile management, offering enhanced security and simplified device management. However, it also introduces challenges, particularly regarding user autonomy and privacy. Understanding these advantages and disadvantages is crucial before removing or bypassing this service.
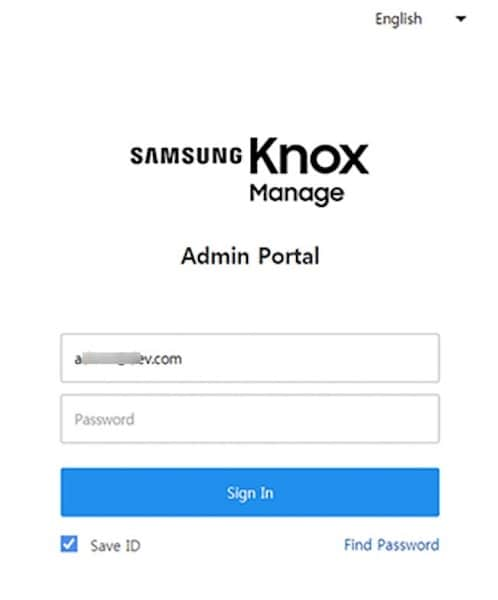
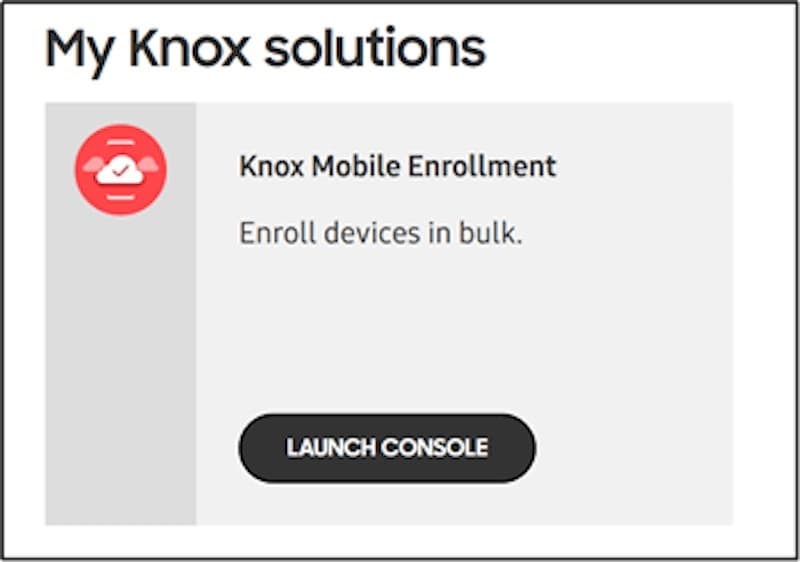
Part 2: How To Remove Knox Enrollment Service on Your Motorola Edge 40 Pro
In most cases, an administrator can only effectively remove the Knox Enrollment Service through the Samsung Knox Portal. This typically requires cooperation from your employer.
Here’s a step-by-step guide to removing itfrom the Admin’s Portal:
- Step 1: Sign in to the Samsung Knox Portal using administrative credentials.
- Step 2: Navigate to Samsung Knox Mobile Enrollment, then click Devices.
- Step 3: Select the Motorola Edge 40 Pro device in question and click Actions.
- Step 4: Choose the Clear Profile option to remove all profiles from the Motorola Edge 40 Pro device. This action will disassociate the Motorola Edge 40 Pro device from any existing Knox configurations.
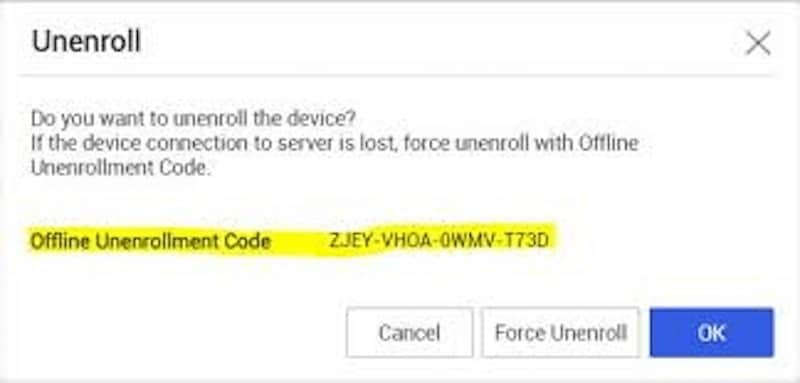
After removing the Motorola Edge 40 Pro device from Knox Enrollment via the admin account, you may still need to uninstall the Knox app from the Android device. This can usually be done through the Motorola Edge 40 Pro device’s settings. Navigate to ‘Apps’ in the settings menu, locate the Knox app, and select ‘Uninstall’ or ‘Disable’. Be aware that this option might not be available on all devices, depending on how Knox was configured.
Rooting and Flashing a New ROM To Remove Knox Enrollment Service
For the more tech-savvy users, another method to bypass Knox Enrollment Service is by rooting the Motorola Edge 40 Pro device and flashing a new ROM. This process involves gaining root access to the Motorola Edge 40 Pro device’s operating system, which allows you to modify the software extensively. After rooting, you can flash a new ROM that doesn’t include the Knox software.
However, this method is risky and not recommended for the average user. It will void your warranty and potentially ‘brick’ your device, rendering it unusable. Furthermore, this action could notify your employer of your attempt to remove Knox, which could have professional repercussions. Proceed with this method only if you know the risks and consequences.
Removing Knox Enrollment Service from your phone is feasible but requires careful consideration, especially in a corporate context. Always ensure you have the necessary permissions and understand the risks of modifying your device’s software.
If You Can’t Use the Above Methods
If none of the above methods are feasible, and you find your phone locked or restricted due to Knox, read through the next section. It will provide additional insights on what to do next.
Part 3: How To Bypass a Locked Phone With a Professional Tool
When faced with a locked phone due to Knox security features, and if conventional methods don’t yield results, turning to a third-party tool can be a viable solution. One such tool known for its efficiency in bypassing phone locks is Wondershare Dr.Fone - Screen Unlock.
Wondershare Dr.Fone is a versatile software suite that tackles various smartphone issues, including unlocking screens. Its Screen Unlock feature is useful for bypassing security barriers without requiring extensive technical knowledge. It hosts several features, such as those you need for data recovery, system repairs, and other smartphone services.
Dr.Fone’s Screen Unlock Feature
The Screen Unlock feature in Dr.Fone is specifically designed to bypass screen locks. Often, you can use it for issues such as forgotten passwords or the like. The great thing is that it can also bypass those locks enforced by Knox. You can do all these without causing data loss or significant changes to your device’s system.

Dr.Fone - Screen Unlock (Android)
The Best UnlockJunky Alternative to Bypass FRP and Solve Your Screen Locks
- Remove all Android screen locks (PIN/pattern/fingerprints/face ID) in minutes.
- Bypass the FRP lock of Samsung without a PIN or Google account.
- Everyone can handle the lock screen without any tech knowledge.
- Provide specific removal solutions to promise good success rate.
4,008,669 people have downloaded it
How To Use Dr.Fone - Screen Unlock
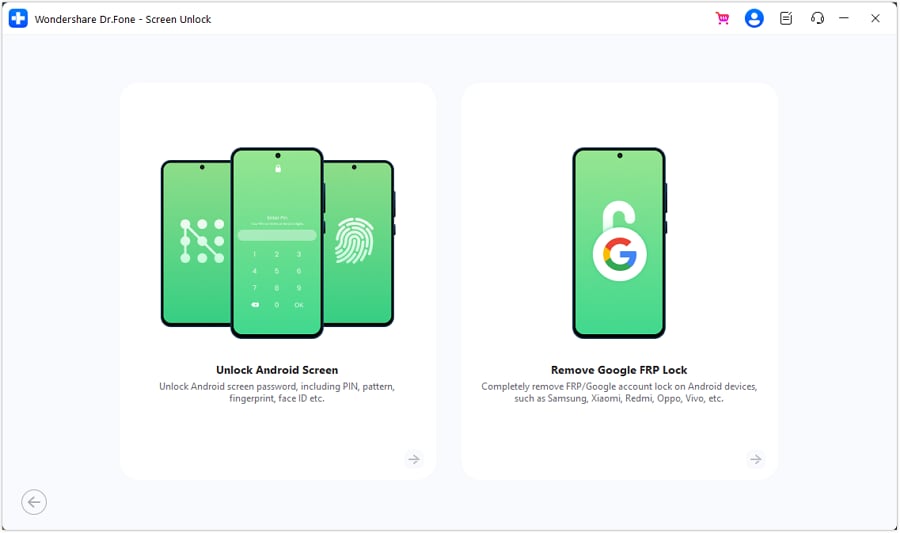
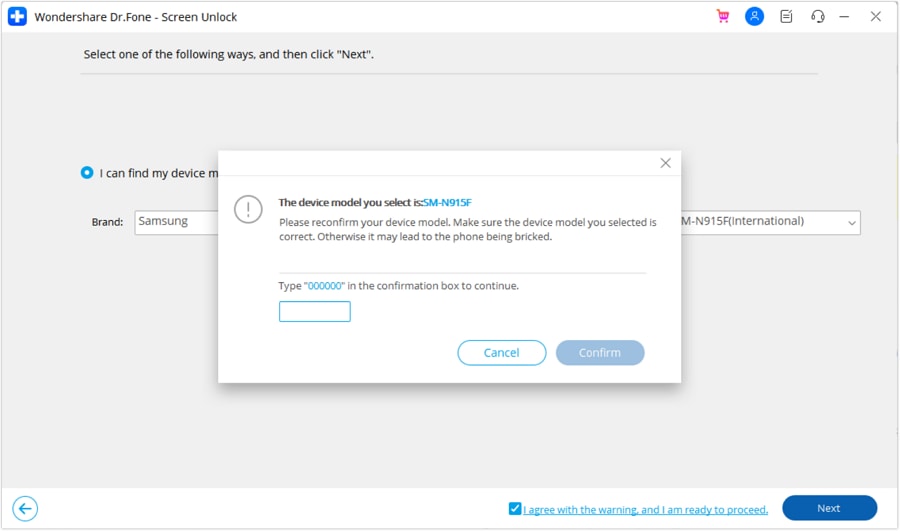
- Step 1: Open Dr.Fone and select the Screen Unlock module under Toolbox. Connect your locked phone to the computer using a USB cable.
- Step 2: On the next pages, select Android > Unlock Android Screen.
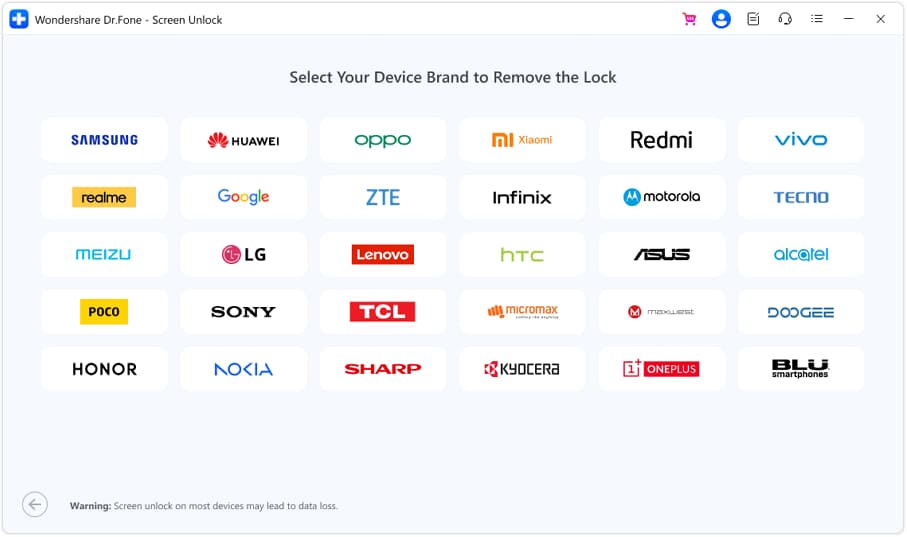
- Step 3: Find the brand of your device.
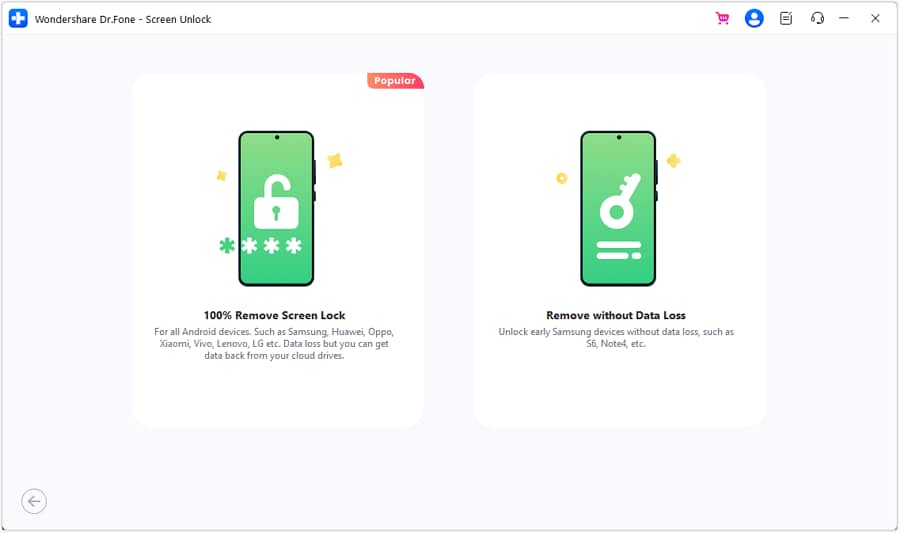
- Step 4: Select Remove without Data Loss.
- Step 5: Enter “000000” to start the process after confirming device details.
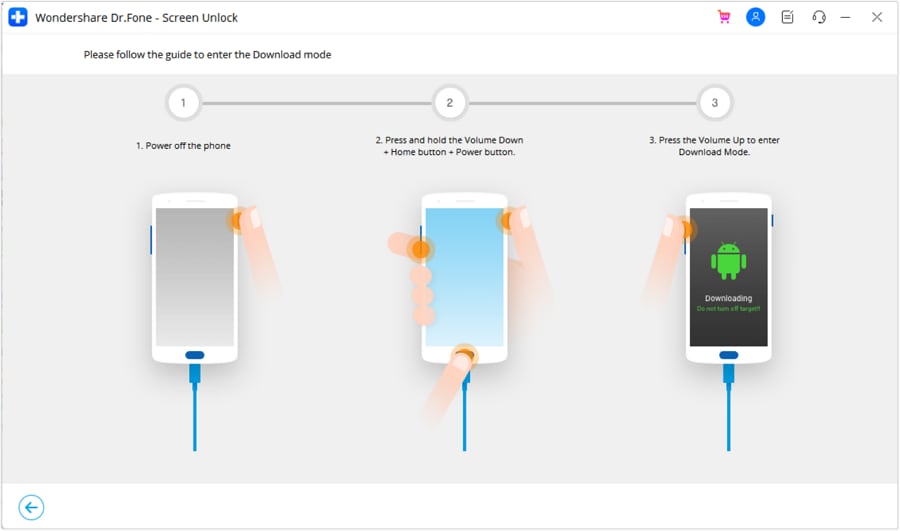
- Step 6: Follow the instructions to put your device into Download Mode.
- Step 7: After the process is completed, click Done. Don’t be afraid to retry the process if it doesn’t work.
If you find yourself locked out of your phone due to Knox and unable to use conventional methods to regain access, Wondershare Dr.Fone offers a reliable and user-friendly alternative. Its Screen Unlock feature is designed to bypass such security features effectively, ensuring you can regain phone access with minimal fuss.
You May Also Interested:
Tutorial to Change Android IMEI without Root
8 Safe and Effective Methods to Unlock Your iPhone Without a Passcode
How to Unlock OPPO Phone Without Password?
Conclusion
In this article, you’ve explored the intricacies of the Knox Enrollment Service and the steps to remove or bypass it. Key takeaways include understanding what Knox is and its removal or bypass methods. However, securing authorization from your organization or phone provider is important before proceeding. This precaution is crucial to avoid potential complications.
For those facing a locked phone due to Knox and unable to follow conventional methods, Wondershare Dr.Fone emerges as a reliable solution. Its Screen Unlock feature offers a safe and efficient way to regain access to your device, ensuring you stay connected without compromising security.
Also read:
- [New] 2024 Approved Integrating Twitter Content with Facebook Networks
- [New] Tricks for High-Quality Snapchat Recordings on Phone for 2024
- [Updated] 2024 Approved Elevating Your Vlogs with High-Quality Editing - Premiere Pro Style
- [Updated] The Comprehensive Guide to Adding a Link in Your TikTok Profile
- 7 Ways to Unlock a Locked Asus ROG Phone 7 Ultimate Phone
- Accelerate Tagalog Learning in Minutes, Not Days
- Downloading SamFw FRP Tool 3.0 for Motorola Edge 40 Pro
- How to Unlock a Network Locked Motorola Defy 2 Phone?
- How to Unlock Vivo V27 Pro Phone Pattern Lock without Factory Reset
- In 2024, A Complete Guide To OEM Unlocking on Samsung Galaxy XCover 7
- In 2024, Complete Review & Guide to Techeligible FRP Bypass and More For Oppo A18
- In 2024, How To Easily Unlock Samsung Screen?
- In 2024, How to Unlock Samsung Phone without Any Data Loss
- Leading Linux Editors Top 8 Video Cutters for 2024
- Learn How to Optimize Your Screen Record with Screencastify
- New Online Collage Creators Make Stunning Photo and Video Montages
- Your Complete Guide To Reset Realme 10T 5G | Dr.fone
- Title: In 2024, Top 10 Password Cracking Tools For Motorola Edge 40 Pro
- Author: Peter
- Created at : 2025-01-08 17:42:24
- Updated at : 2025-01-11 19:00:40
- Link: https://android-unlock.techidaily.com/in-2024-top-10-password-cracking-tools-for-motorola-edge-40-pro-by-drfone-android/
- License: This work is licensed under CC BY-NC-SA 4.0.