
How To Enable USB Debugging on a Locked Lava Yuva 2 Phone

How To Enable USB Debugging on a Locked Lava Yuva 2 Phone
Unlocking your Android’s potential goes beyond its surface features. Understanding USB debugging is key to troubleshooting and maximizing your device’s capabilities. In simple terms, USB debugging allows deeper access to your phone’s functionalities, aiding in software development and data recovery.
However, enabling USB debugging becomes crucial yet challenging when your phone is locked. This article delves into this necessity, explaining how to enable USB debugging on locked phones, especially for Android users. Unravel the mystery behind this essential feature, empowering yourself to navigate through locked phone scenarios effortlessly.
Part I. Challenges in Enabling USB Debugging on a Locked Android Phone
USB debugging is a nifty tool that lets you peek behind the scenes of your Android phone’s software. It’s like having a secret key that unlocks deeper access to your device, enabling tasks like software tweaking, app testing, and even data recovery.

Challenges in Enabling USB Debugging on a Locked Phone
Outlined below are some of the barriers, scenarios, and limitations, shedding light on the challenges that make USB debugging seemingly impossible.
- **Locked-out access.**When your phone is locked, gaining access to the settings becomes a roadblock to enabling USB debugging.
- **Limited functionality.**The phone’s locked state restricts the usual methods of accessing developer settings and USB debugging options.
- **Security measures.**For security reasons, most devices limit access to sensitive settings when the phone is locked, making it tricky to enable USB debugging.
Scenarios Requiring USB Debugging on a Locked Phone
Unlocking your phone’s potential becomes crucial in moments of crisis. Explore below some of the scenarios where enabling USB debugging on a locked Android device becomes your beacon of hope:
- **Data recovery.**Imagine accidentally locking yourself out of your phone with important data inside. Enabling USB debugging could be your ticket to retrieve that precious information.
- **Software troubleshooting.**Sometimes, a locked phone might need software fixes or troubleshooting that requires USB debugging to access certain tools.
- **Device testing.**For developers or tech-savvy users, testing new apps or debugging software issues often demands enabling USB debugging, even when the phone is locked.
Part II. How To Enable USB Debugging on Locked Phones
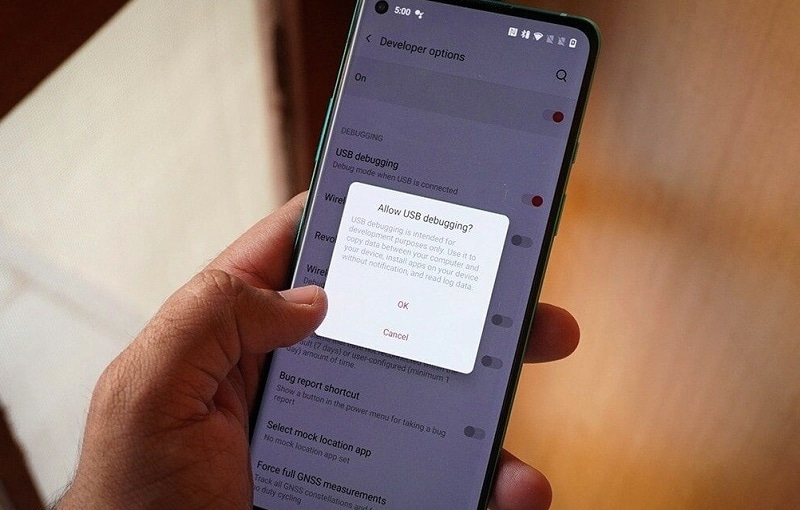
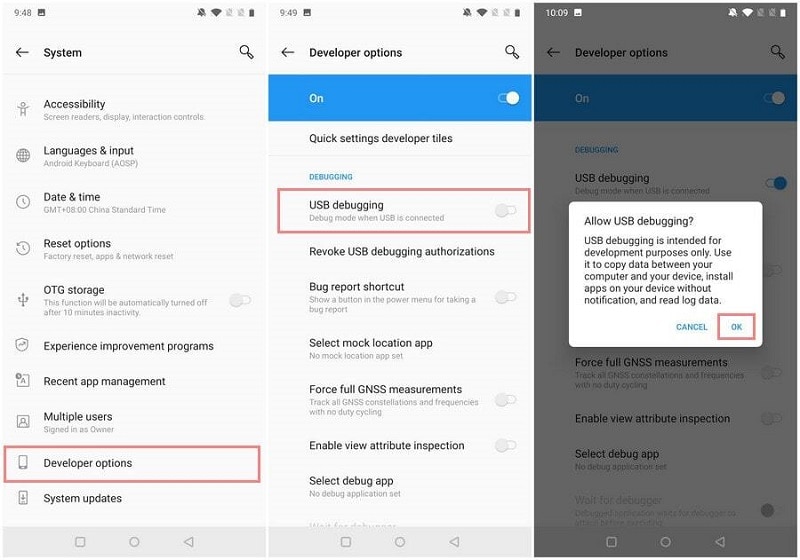
This section outlines the traditional method of enabling USB debugging on an Android phone. Stay tuned and check out the steps below:
- Step 1: Unlock your device**.** If needed, enter your phone’s passcode or pattern to gain access to the Settings.
- Step 2: Go to Settings, scroll down to About Phone, and tap on Build number seven or eight times to unlock the Developer Options.

Step 3: Once unlocked, return to Settings, find Developer Options (usually at the bottom), and enter the menu. Enable USB Debugging by tapping OK once the Allow USB Debugging? message appears.
However, what if your phone remains locked, making these steps impossible? Such a case calls for an alternative solution. Fortunately, there is one tool that is fully reliable when it comes to unlocking locked mobile devices. Dr.Fone - Screen Unlock (Android) can help bypass these challenges and enable USB debugging on a locked Android phone effortlessly. So, buckle up as the next section unravels the secrets to unlock your device’s potential!
Part III. Seamlessly Unlock Your Android With a Professional Resolution
Enabling USB debugging on a locked phone can feel like navigating a maze with no clear exit. Sometimes, despite your best efforts, the traditional method fails to grant access. Fret not! There’s a smoother path that unlocks your phone and eases the USB debugging hurdle.
Why Unlocking First Makes Sense
Attempting to enable USB debugging on locked phones can hit roadblocks. That’s why unlocking your device first becomes a game-changer. Dr.Fone – Screen Unlock (Android) is the hero of this story, simplifying the process and ensuring a hassle-free experience.
Key Features and Benefits
Check out the amazing key features and benefits of Dr.Fone – Screen Unlock that fits Android devices:
- **Data safety and reliability.**Your data’s security remains paramount. With Dr.Fone – Screen Unlock, your device’s integrity and precious data stay safeguarded throughout the unlocking process.
- Dr.Fone - Screen Unlock is compatible with a wide range of Android devices, irrespective of brand or model, ensuring accessibility for various users.
- It’s not just about unlocking a locked screen; Dr.Fone offers multiple unlock modes tailored to different scenarios, whether a forgotten password, PIN, pattern, or fingerprint issue.
- **High success rate.**With a high success rate in unlocking locked screens, Dr.Fone - Screen Unlock provides a reliable solution, even for complex lock scenarios.
- **No data loss.**Users can rejoice in the fact that the unlocking process doesn’t compromise data integrity. Your photos, messages, and apps remain untouched and secure.
- **Ease of use.**The software is designed for simplicity, making the unlocking process accessible to users with varying levels of technical expertise.
Tips: Forget your device password and can’t get access to it? No worries as Dr.Fone is here to help you. Download it and start a seamless unlock experience!
Guide To Unlock Your Lava Yuva 2 With Dr.Fone – Screen Unlock (Android)
Below are the steps on how you can unlock your Android device using Dr.Fone:
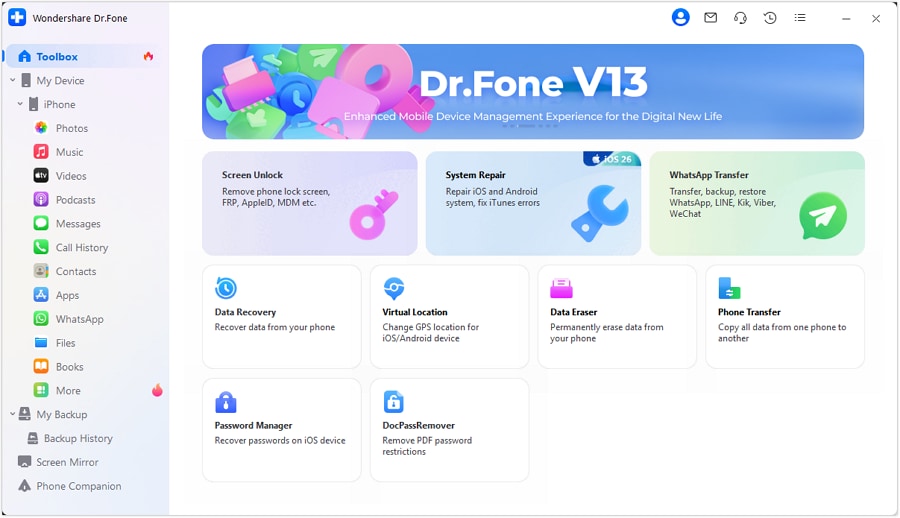
Step 1: Get the most recent version of Wondershare Dr.Fone and connect your Android device to your computer via a USB cord. After connecting, access the unlock screen tool by going to the Toolbox and then selecting Screen Unlock.
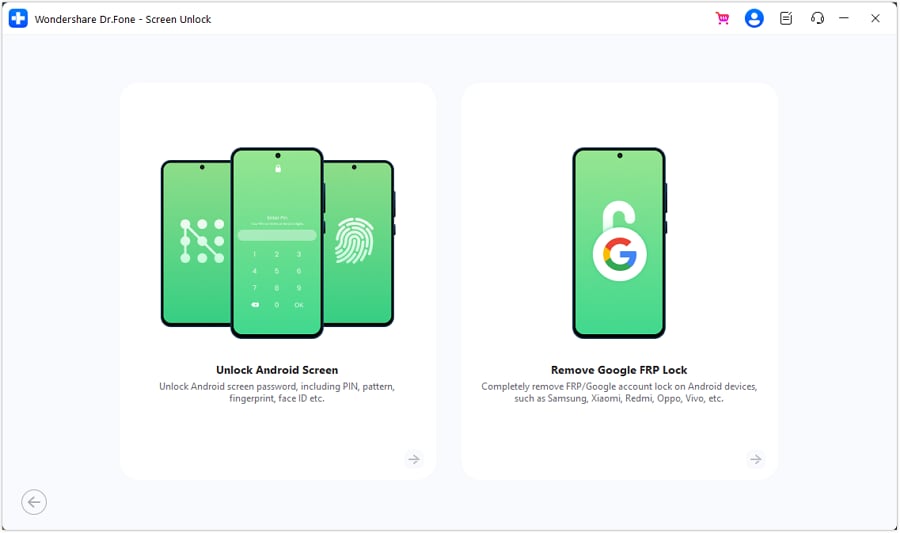
Step 2: Once prompted, choose Android to unlock your Android screen lock. On the following screen, you’ll see two options; choose Unlock Android Screen.
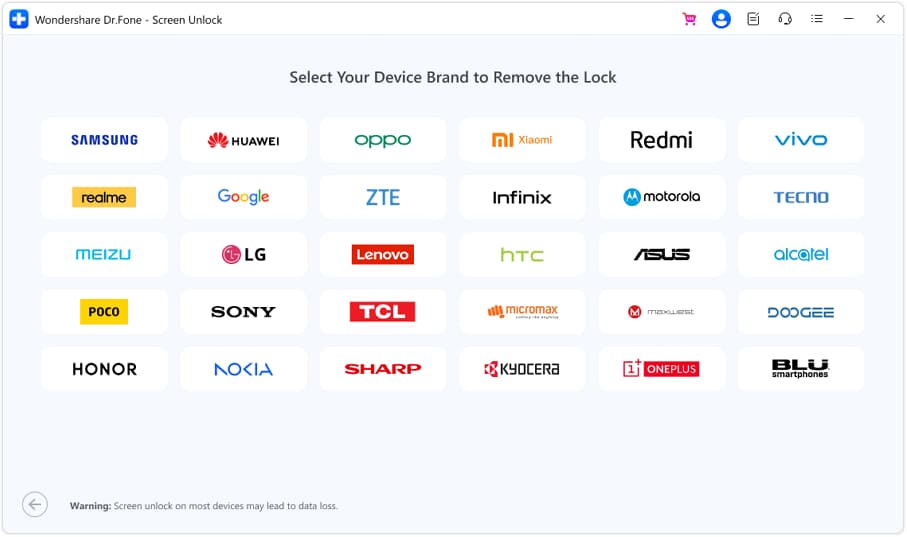
- Step 3: After that, you’ll be taken to a new screen where you can choose the brand of your mobile device.
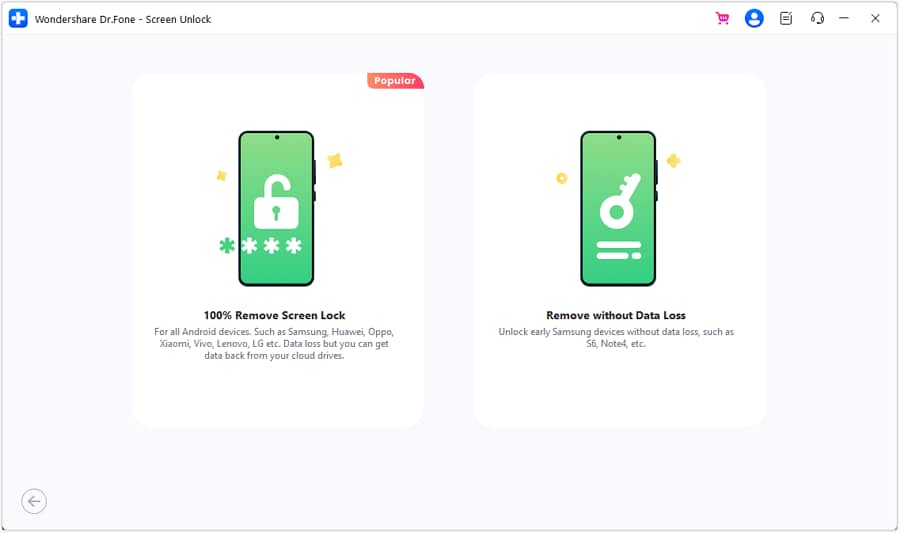
- Step 4: Once done, click the Remove without Data Loss button from the two options presented on the screen.
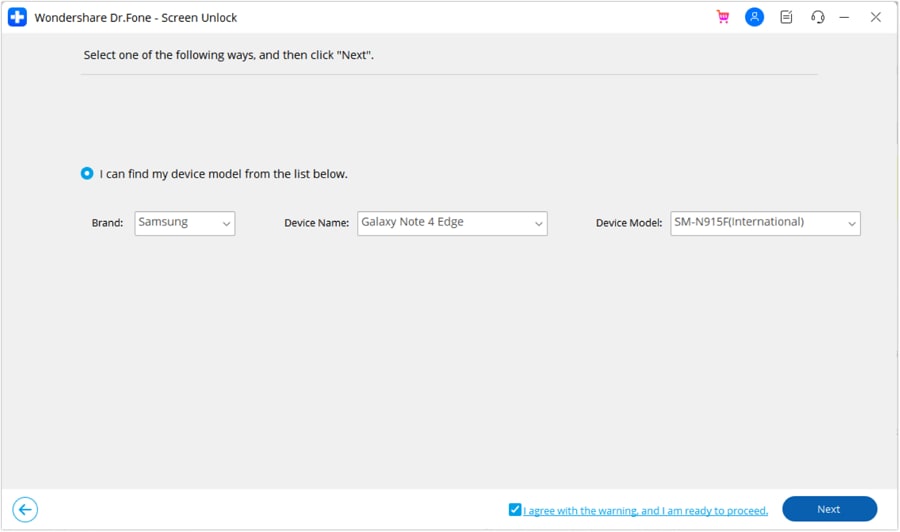
- Step 5: Unlocking the Android screen requires choosing the Brand, Device Name, and Device Model next. Enable the option that says I agree with the warning, and I am ready to proceed by clicking the corresponding checkbox. To proceed with unlocking the screen, click Next.
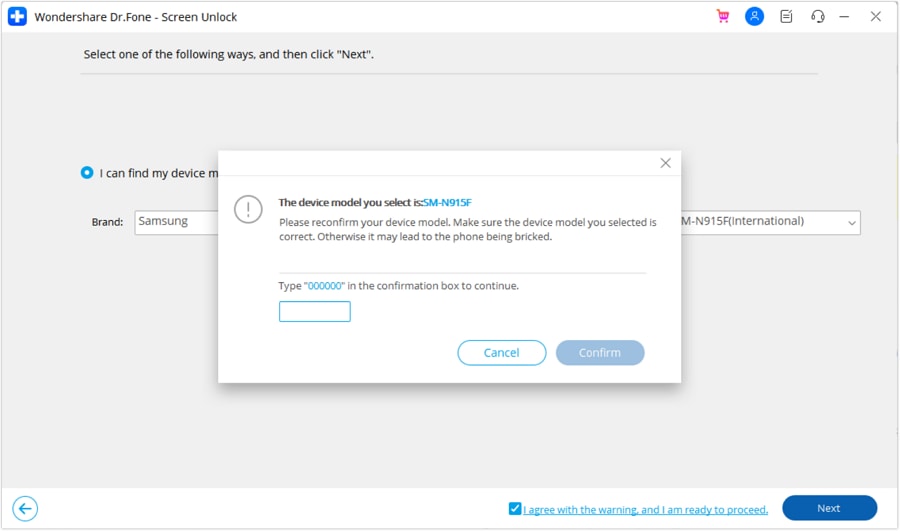
- Step 6: Type 000000 when asked to confirm the process. After entering the code, click Confirm to run the program.
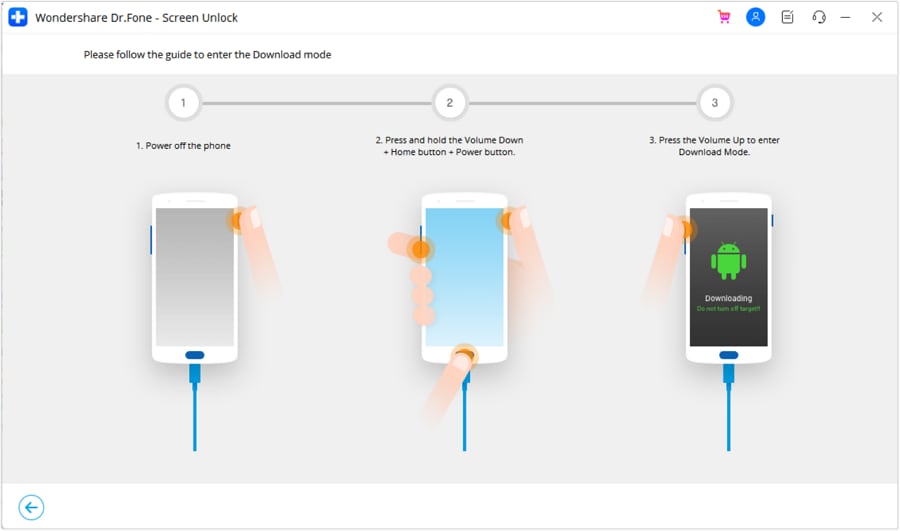
- Step 7: Once you’ve recognized your Android device’s model, Dr. Fone will walk you through entering Download Mode. Following the on-screen prompts will take you directly to the next screen. It then depicts the progress of the screen unlocking procedure, in which the platform’s required drivers and configuration files are downloaded.
- Step 8: A new screen will appear, indicating the process has been completed. Click Done if your device’s screen unlock issue has been successfully fixed. If not, click the Try Again button.
Dr.Fone – Screen Unlock (Android) acts as your trusty guide, leading you through the maze of locked screens and inaccessible settings. It unlocks your phone first and enables USB debugging without the frustrating barriers.
Learn More About Android Unlock:
Samsung Unlock Codes to Unlock Samsung Phones [2024 Updated]
Unlocking Your Realme Phone Made Easy: No Data Loss!
The Best Android Unlock Software of 2024
Conclusion
In face of locked screens, USB debugging is a beacon of access and troubleshooting for your Android device. Remember, enabling USB debugging on a locked phone is crucial, opening doors to unforeseen solutions. However, what if you want to enable USB debugging on locked phones, but the process gets messy?
Then, it’s time to consider Dr.Fone - Screen Unlock (Android). It effortlessly paves the way to enable USB debugging on locked phones. By ensuring your device’s security and accessibility, even in locked states, Dr.Fone empowers you to navigate through obstacles, safeguarding your data while unlocking endless possibilities.
How To Track IMEI Number Of Lava Yuva 2 Through Google Earth?
When losing your phone, having a reliable tool at your fingertips can make all the difference. That tool is IMEI tracking, your secret weapon for locating your lost or stolen device. IMEI is a unique number that every mobile device possesses. It’s like a fingerprint for your phone.
Now, the question is, is it possible to track an IMEI number through Google Earth? This question has sparked much debate on the internet, so this article aims to find it out. Keep reading and learn the secrets of Google Earth IMEI trackers.

Part 1: How To Track Your Lava Yuva 2 on Google Earth
This Google Maps IMEI number tracking issue has caused quite a buzz and controversy on the internet. It has raised many concerns regarding the safety and privacy of every smartphone user. To tell you the truth, Google Earth lacks IMEI location data and does not provide such capabilities. Thus, there is no truth in tracking IMEI numbers through Google Earth.
However, if you have access to a cell phone’s GPS coordinates or the location of a cell tower to which it is linked, you can use Google Earth to follow its location.
How To Locate a Smartphone Using Google Earth
Many current smartphones include GPS receivers that allow them to pinpoint their exact location. If you know the phone’s GPS coordinates, you can plug them into Google Earth to see where it is on the map.
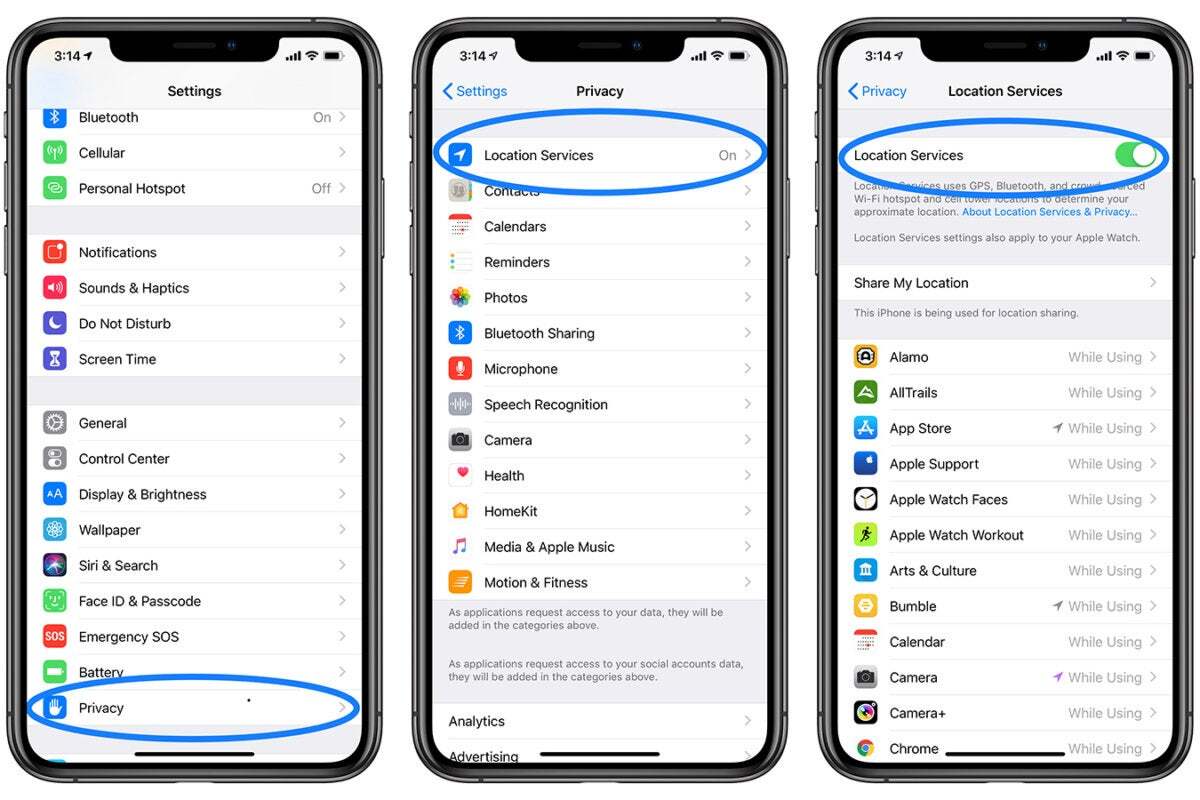
- Step 1: This process won’t be possible if your location services are not enabled on your phone. To do this, navigate to Settings, then Location on Android, and Settings > Privacy > Location Services on iOS.
- Step 2: Google Earth can be downloaded and installed on your computer or mobile device. It works with Windows, macOS, Android, and iOS. Download it from your device’s Google Earth website or the app store.
- Step 3: Sign in to Google Earth using the Google Account linked to the phone you want to track. This step is required to acquire location data and monitor IMEI numbers using Google Earth.
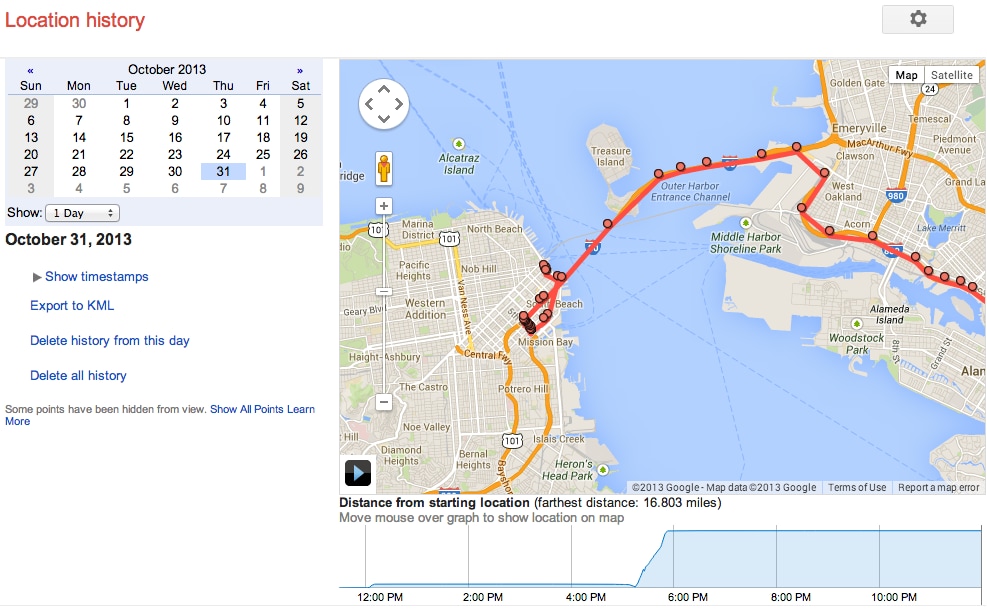
- Step 4: Launch Google Earth on your computer or mobile device, then select Your timeline from the Google Maps menu. The operation will take you to the Google Maps Timeline page.
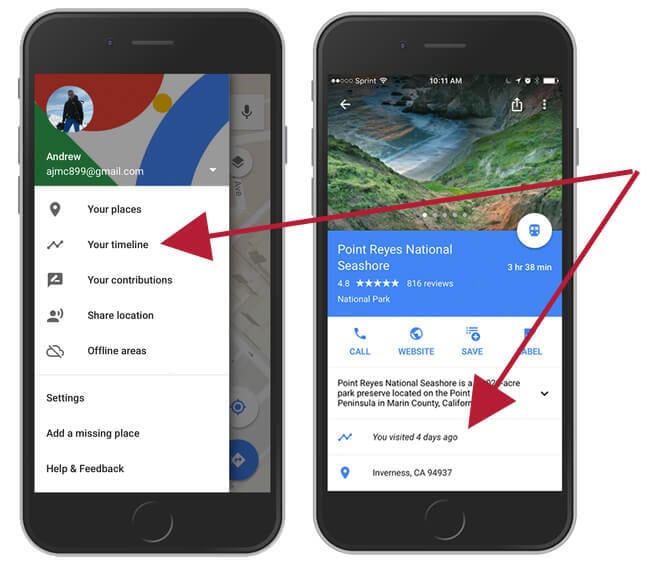
- Step 5: Select the day you wish to see the phone’s location history. Choose the Lava Yuva 2 device you want to track from the dropdown menu if you have numerous devices linked to the same account. The timeline displays the selected device’s location history for the set date. Examine the locations visited, the routes taken, and the time spent at each spot. For further information, select a certain location or time.
Note: Google Earth does not support real-time location tracking by default. You can use the Find My Device function on Android or Find My on iOS instead if you want to track your phone’s real-time location.
Part 2: Google Earth Alternatives: Track Phone Using IMEI Number
Now that you know the truth behind tracking an IMEI number through Google Earth, let’s talk about other ways to track your phone using your IMEI number. This section will discuss some of your other options when it comes to IMEI number location tracking.
Method 1: Using a Third-Party App
If you have the IMEI number of the stolen device, you can track the phone using IMEI for free utilizing various tools available online.
- Step 1: In the app store, search for “IMEI tracker” and download the IMEI tracking app you wish to install on your phone.
- Step 2: Open the app and follow the in-app guide on how to use it.
Note: Most of the apps require authorization access to your phone. Some also provide a feature where you may send an SMS or a command to get the lost phone’s location.
Method 2: Online IMEI Tracking
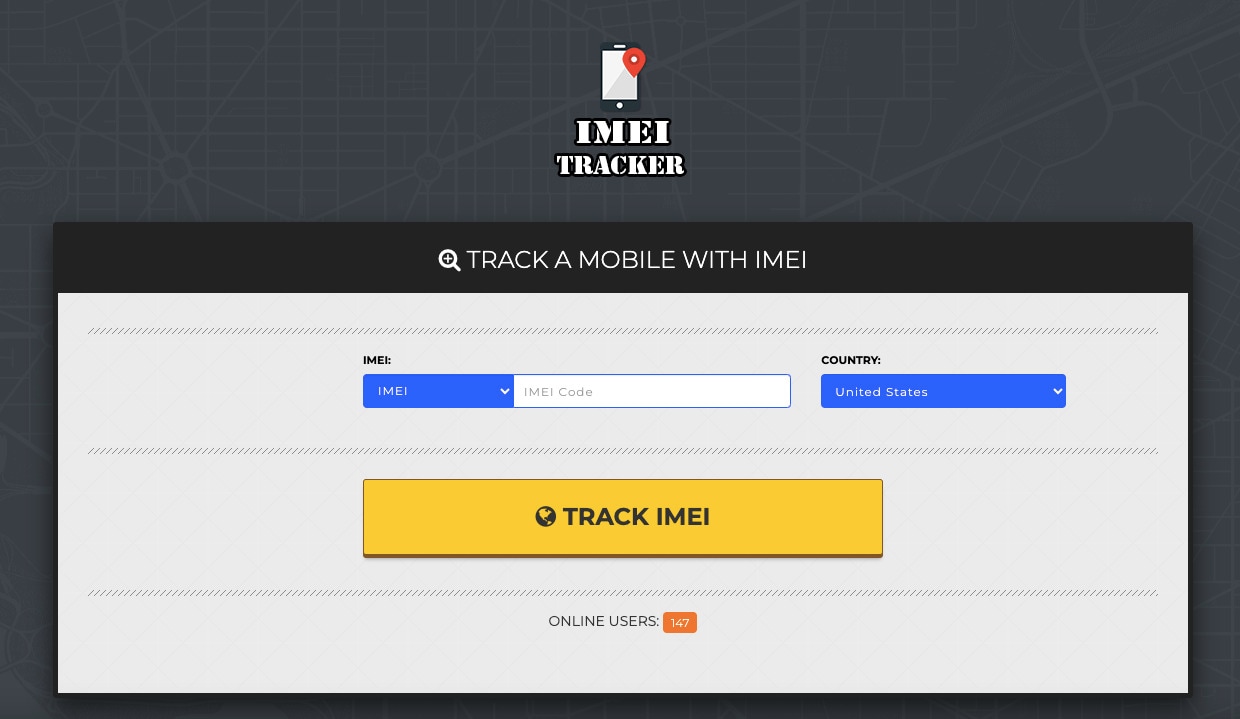
In certain situations, an online platform is preferable to a mobile app. For your convenience, a free online platform for tracking a phone using its IMEI number is featured below:
IMEI TRACKER
The online IMEI TRACKER is simple to use. After searching an IMEI tracker in Google and opening its website, please enter a valid IMEI code in its search bar and specify the country where your cell phone was first registered. After that, you have to wait for a few moments, and then you may view the phone’s location status and determine whether it is lost or stolen.
Pros and Cons of IMEI Trackers: Apps and Online Platforms
Now that you know there are still methods to track a phone using an IMEI number, it’s also important to weigh their pros and cons. See the list presented below:
Pros
Check out the advantages of using IMEI trackers below:
- **Lost or Stolen Device Recovery.**The primary benefit of an IMEI tracker is its ability to help locate a lost or stolen mobile device. That can be crucial for recovering your valuable device.
- **No Need for Special Apps.**Unlike many other tracking methods, IMEI tracking doesn’t require any special apps or software to be installed on the Lava Yuva 2 device you want to track. It relies on the unique IMEI number of the Lava Yuva 2 device.
- IMEI Tracker is compatible with many mobile devices, including smartphones and feature phones. It’s not limited to a specific operating system or brand.
Cons
Below are the drawbacks of using IMEI trackers:
- **Privacy Concerns.**IMEI tracking can raise privacy concerns, as it involves tracking the location of a mobile device. It’s essential to use this technology responsibly and only for legitimate purposes.
- **Internet and Network Dependency.**IMEI tracking depends on the Lava Yuva 2 device being connected to the internet or a mobile network. If the Lava Yuva 2 device is turned off, in airplane mode, or disconnected, tracking may be impossible.
- **Inaccuracies in Remote Areas.**IMEI tracking can be less accurate or even unavailable in remote or rural areas with poor network coverage.
In summary, an IMEI tracker can be a valuable tool for locating lost or stolen mobile devices with its location accuracy and compatibility with various devices. However, it comes with limitations related to privacy and network dependency.
Bonus: An Effective Method for Other iPhone Issues Like Locked Screens
In the previous sections, this article delved into IMEI tracking, which helps you accurately locate your lost or stolen phone. However, imagine this scenario: you’ve found your long-lost iPhone, but there’s a problem. You can’t remember the password, PIN, or pattern to unlock it. So this time, let’s go over one of the most common issues smartphone owners encounter: being locked out of their devices.
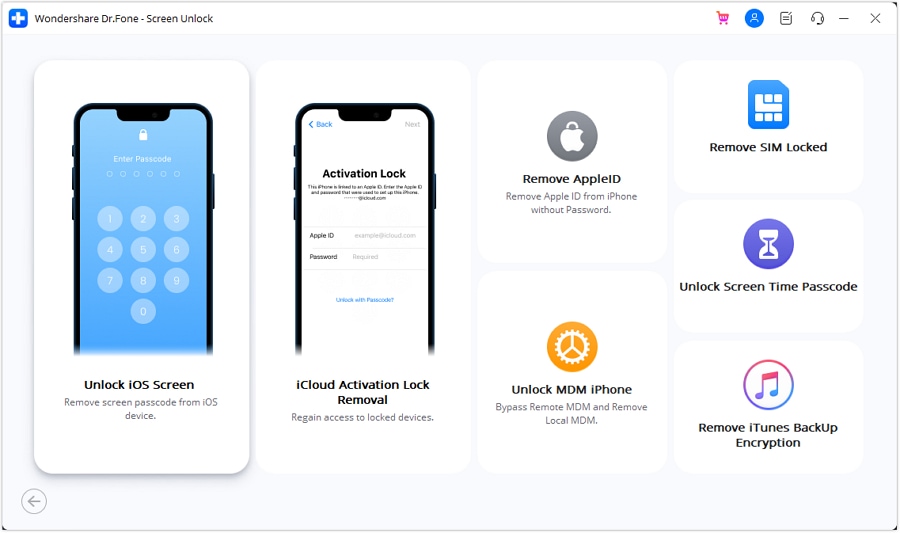
Introducing Wondershare Dr.Fone – Screen Unlock (iOS): Your iPhone Savior
There are numerous scenarios where one may forget the passcode on their iOS device. While many people dismiss their phones as useless, there are ways to unlock iPhones correctly. And that’s where Dr.Fone - Screen Unlock (iOS) comes to the rescue. It’s like the locksmith for your phone’s digital lock.

Why Dr.Fone - Screen Unlock Is Your Go-To Solution
Let’s discuss why Dr.Fone - Screen Unlock is a game-changer in unlocking phone, especially when using your IMEI number.
- **User-Friendly Interface.**Fone - Screen Unlock boasts an interface designed with you in mind. You don’t need to be a tech guru to use it. The steps are straightforward, making the whole process hassle-free.
- **Wide Compatibility.**One of the best things about Dr.Fone - Screen Unlock is its compatibility with various mobile devices. It doesn’t matter if you’re using an Android or iOS device; this tool has you covered. It’s like having a universal key to open many locks.
- **Safe and Secure.**Security is a top priority when it comes to your phone. Dr.Fone - Screen Unlock ensures that your data remains safe during unlocking. Your personal information won’t be compromised.
Step-by-Step Guide
Now, let’s dive into how to use Dr.Fone - Screen Unlock to unlock your phone easily :
- Step 1: After downloading and installing Wondershare Dr.Fone on your PC, click Toolbox, click Screen Unlock, then choose iOS. In the window that appears, click the Unlock iOS Screen button.
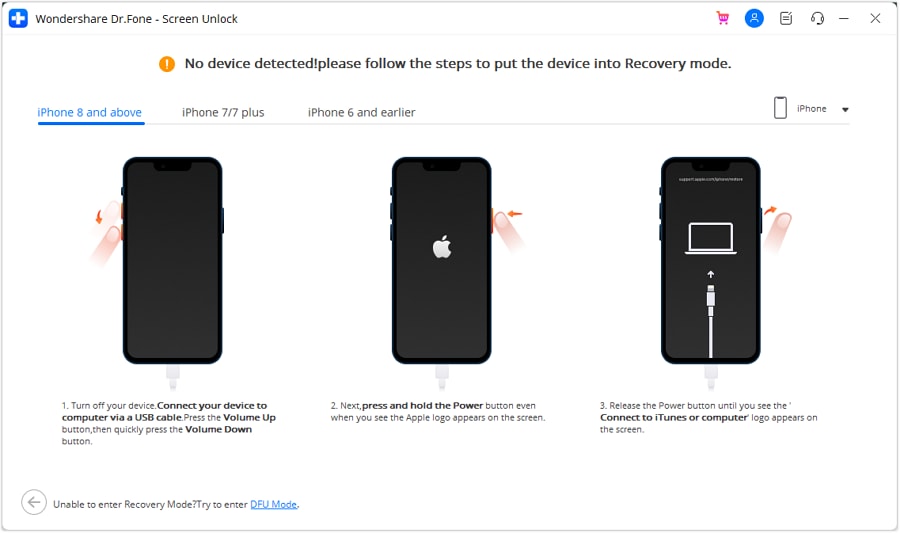
- Step 2: On the next screen, select Start to begin the unlocking procedure for the iOS device. Make sure that your device’s battery levels are enough.
- Step 3: After that, you should set your iDevice into Recovery Mode. Follow the on-screen instructions to put your iDevice into the appropriate mode for your model. If Recovery Mode does not work, click the Try DFU Mode button at the bottom to access the instructions for entering the iDevice into DFU mode.
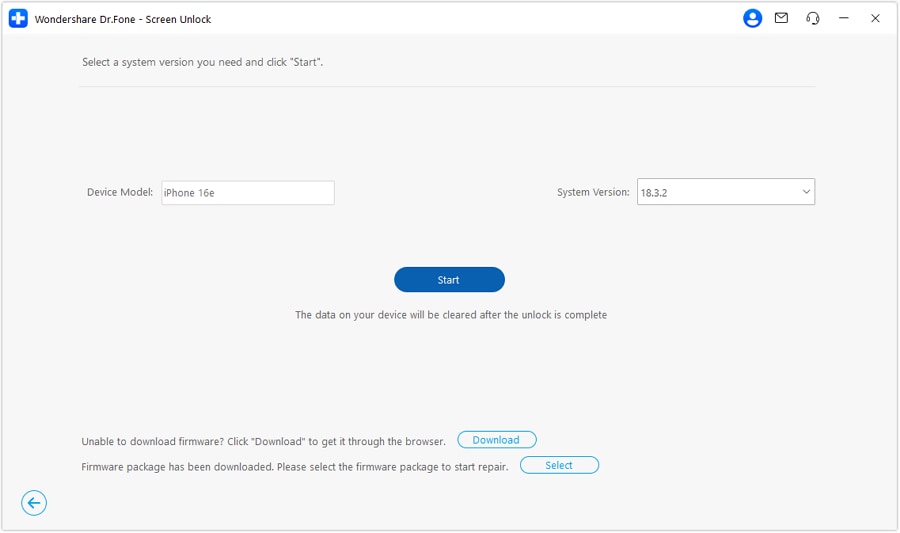
- Step 4: After the user successfully enters their iDevice into Recovery Mode, the platform automatically recognizes the Device Model and shows it in the appropriate section. Modify the model and select the System Version to meet your needs if necessary. After that, select Start to begin unlocking your device’s screen.
- Step 5: The following screen reveals the status of the iOS firmware download on the platform. If you want to stop the procedure, click the Stop button. In cases when the iOS firmware is downloading slowly on the platform, utilize the Copy button to copy the URL for manually downloading the iOS firmware.
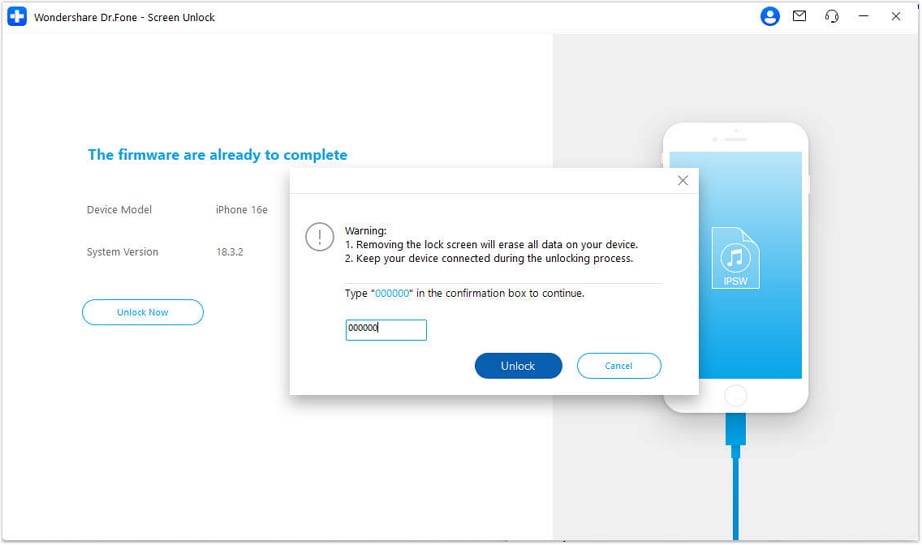
- Step 6: After successfully downloading the iOS firmware, it is confirmed and displayed on the next screen. Continue by clicking the Unlock Now button to begin the unlocking procedure.
- Step 7: A prompt window displays on the screen, asking for procedure confirmation. Enter the indicated code and tap Unlock to proceed with the final result.
- Step 8: The next screen displays the unlocking iOS device’s progress bar. Keep in mind that the Lava Yuva 2 device must be connected at all times; otherwise, it will brick.
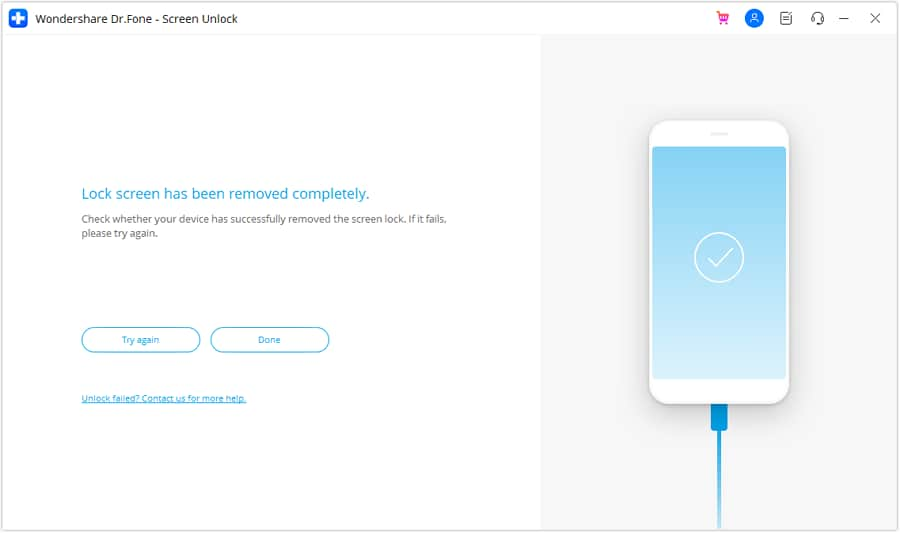
- Step 9: Once the iDevice has been successfully unlocked, click the Done button to complete the process. If your iDevice is still locked, click Try Again to restart the process.
Conclusion
This article explored the incredible world of IMEI tracking, a powerful tool for locating lost or stolen phones. You’ve learned that your IMEI number is capable of helping you pinpoint your device’s location, but tracking IMEI numbers through Google Earth is impossible.
But that’s not all. This article also introduced and divulged an amazing and reliable tool for unlocking an iPhone. So, the next time you’re in a tight spot with a locked screen, remember that Dr.Fone - Screen Unlock (iOS) is the best software you should get your hands on.
Top 10 Password Cracking Tools For Lava Yuva 2
What is password cracking?
Password cracking process involves recovering a password from storage locations or from data, transmitted by a computer system on network. Password cracking term refers to group of techniques used to get password from a data system.
Purpose and reason of password cracking includes gaining an unauthorized access to a computer system or it can be recovery of forgotten password. There might be another reason of using password cracking technique that is for testing password strength so hacker could not hack into system.
Password cracking is normally performed thought repetitive process in which computer applies different combinations of password till the exact match.
Brute Force Password Cracking:
Term brute force password cracking may also be referred as brute force attack. Brute force password cracking is respective process of guessing password, in this process software or tool creates a large number of password combinations. Basically it’s a trail-and-error technique used by software to obtain password information from system.
A brute force attack are normally used by hackers when there is no chance of taking advantage of encrypted system weakness or by security analysis experts to test an organization’s network security .This method of password cracking is very fast for short length passwords but for long length passwords dictionary attack technique is normally used.
Time taken by brute force password cracking software to crack password is normally depend upon speed of system and internet connection.
GPU Password Cracking:
GPU is graphics processing unit, sometimes also called visual processing unit. Before talking about GPU password cracking we must have some understanding about hashes . When user enter password the password information stored in form of computer hashes using the one-way hashing algorithm.
In this password cracking technique using GPU software take a password guess and look through hashing algorithm and compare it or match it with the existing hashes till the exact match.
GPU can perform mathematical functions in parallel as GPU have hundreds of core that gives massive advantage in cracking password. GPU is much faster than CPU so that’s the reason of using GPU instead of CPU.
CUDA Password Cracking:
CUDA Compute Unified Device Architecture is a model for programming and a platform that perform computations in parallel, created by NVIDIA for graphic processing.
CUDA Password cracking includes cracking passwords using Graphics card which have GPU chip, GPU can perform mathematical functions in parallel so the speed of cracking password is faster than CPU.GPU have many 32bit chips on it that perform this operation very quickly.
We can easily access CUDA through libraries, directives and with the help of different programming languages that includes C, C++ and FORTRAN.
Password Cracking Tools
Given below is the list of Top10 Password cracking tools.
1. Cain and Abel : Top password cracking tool for Windows
Cain & Abel is one of the top cracking tool for password cracking and password recovery for Windows OS.
Cain & Abel can use techniques of Dictionary Attack, Brute-Force and Cryptanalysis attacks to crack encrypted passwords. So it only uses the weakness of system to crack password. GUI Interface of software is very simple and easy to use. But have availability limitation, tool only available for window based systems .Cain & Abel tool have many good features some of the features of tool are discussed below:
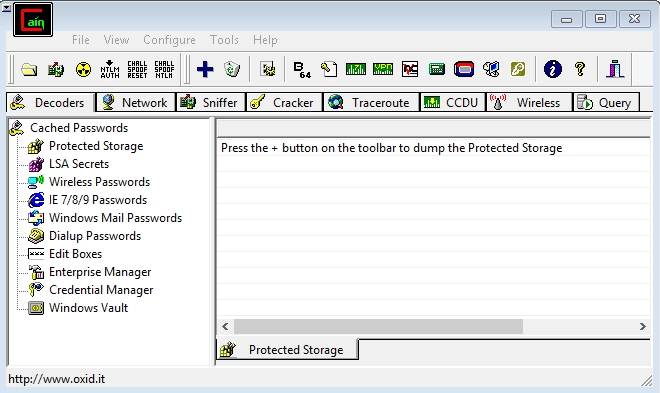
Features of Cain & Abel:
- Used for WEP (Wired Equivalent Privacy) cracking
- Have ability to record conversation over IP
- Cab be used as Network Password Sniffer
- Ability to resolve addresses IP to MAC.
- Can crack verity of hashes including LM and NT hashes, IOS and PIX hashes, RADIUS hashes, RDP passwords, and lots more than that.
Site for Download:
2. John the Ripper : Multi-platform, Powerful, Flexible password cracking tool
John the Ripper is a free multi or cross platform password cracking software. Its called multi platform as it combines different password cracking features into one package.
It’s primarily used to crack weak UNIX passwords but also available for Linux, Mac, and Windows. We can run this software against different password encryptions including many password hashes normally found in different UNIX versions. These hashes are DES, LM hash of Windows NT/2000/XP/2003, MD5, and AFS.
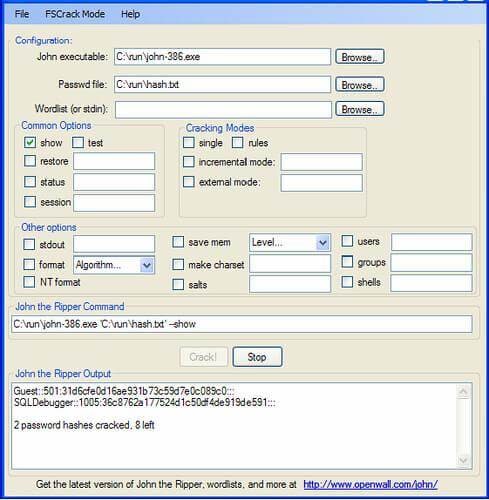
Features of John the Ripper
- Supportive with Brute force password cracking and dictionary attacks
- Multi platform
- Available free for use
- Pro version is also available with additional features
Site for Download:
3. Aircrack : Fast and effective WEP/WPA cracking tool
Aircrack is a combination different tools used for Wifi, WEP and WPA passwords cracking. With the help of these tools you can crack WEP/WPA passwords easily and effectively
Brute force, FMS attack, and dictionary attacks techniques can be used to crack WEP/WPA passwords. Basically it collects and analyzes encrypted packets then using its different tool crack password out of the packets. Although aircrack is available for Windows but there are different issues with this software if we use this in Windows environment, so it’s best when we use it in Linux environment.
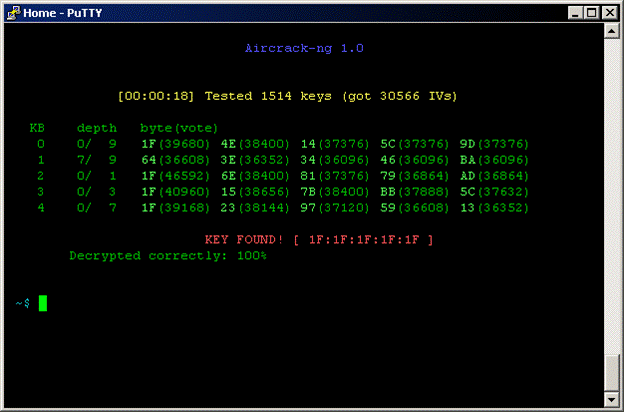
Features of Aircrack
- Supportive with both Brute force and dictionary attacks cracking techniques
- Available for Windows and Linux
- Available in live CD
Site for Download:
4. THC Hydra : Multiple services supportive, Network authentication cracker
THC Hydra is a supper fast network password cracking tool. It uses network to crack remote systems passwords.
It can be used to crack passwords of different protocols including HTTPS, HTTP, FTP, SMTP, Cisco, CVS, SQL, SMTP etc. It will give you option that you may supply a dictionary file that contains list of possible passwords. It’s best when we use it in Linux environment.

Features of THC Hydra
- Fast cracking speed
- Available for Windows, Linux ,Solaris and OS X
- New modules can be added easily to enhance features
- Supportive with Brute force and dictionary attacks
Site for Download:
https://www.thc.org/thc-hydra/
5. RainbowCrack : New Innovation in Password Hash Cracker
RainbowCrack software uses rainbow tables to crack hashes, in other words we can say it uses process of a large-scale time-memory trade for effective and fast password cracking.
Large-scale-time-memory-trade-off is a process of computing all hashes and plain text using a selected hash algorithm. After calculations, obtained results are stored in the tables called rainbow table. Process of creating rainbow tables is very time consuming but when its done software works very fast.
Password cracking using rainbow table is faster than the normal brute force attack method. It’s available for Linux and Windows operating system.
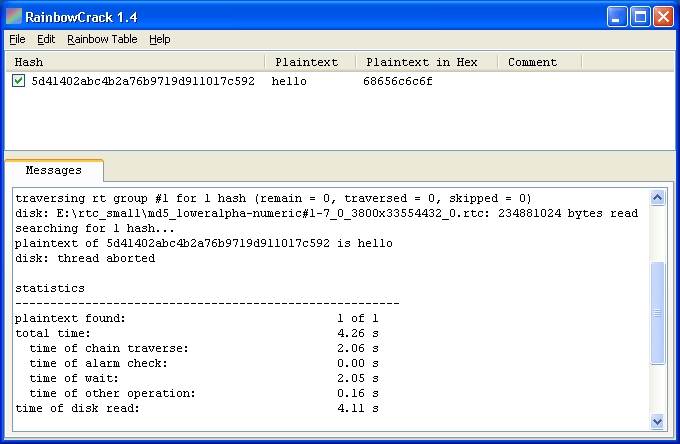
Features of Rainbow Crack
- Support verity of Rainbow tables
- Runs on Windows (XP/Vista/7/8) and Linux operating systems (x86 and x86_64)
- Simple in use
Site for Download:
http://project-rainbowcrack.com/
6. OphCrack : Tool for Windows password cracking
OphCrack used to crack Windows user passwords with the help of rainbow tables that are available in a bootable CD.
Ophcrack is completely free to download, Windows based password cracker that uses rainbow tables to crack Windows user passwords. It normally cracks LM and NTLM hashes. Software has simple GUI and can runs on different platforms.
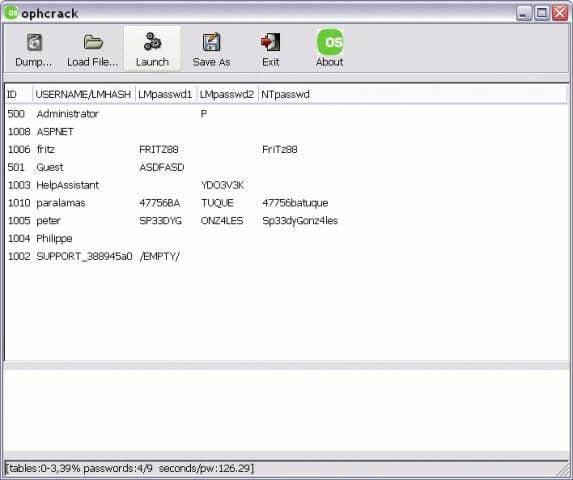
Features of OphCrack
- Available for Windows but also available for Linux, Mac, Unix, and OS X
- Uses for LM hashes of Windows and NTLM hashes of Windows vista.
- Rainbow tables available free and easily for Windows
- To simplify the process of cracking Live CD is available
Site for Download:
http://ophcrack.sourceforge.net/
7. Brutus : A brute force attack cracker for remote systems
Brutus is the fastest, most flexible, and most popular software used to crack remote system passwords. It guess password through applying different permutations or by using a dictionary.
It can be used for different network protocols including HTTP, FTP, IMAP, NNTP and other types such as SMB, Telnet etc. It also gives you facility of creating your own authentication type. It also includes extra options of load and resume, so process can be paused when required and you can resume process when you want.
It is only available for windows operation systems. Tool has a limitation that it has not been updated since 2000.

Features of Brutus
- Available for Windows
- Can be used with different network protocols
- Tool have many good extra features
- Support SOCK proxy for all types of authentications
- Capability of error handling and recovery
- Authentication engine is multi stage
Site for Download:
8. L0phtCrack : Smart tool for Windows password recovery
Just like OphCrack tool L0phtCrack is also a Windows passwords recovery tool uses hashes to crack passwords, with extra features of Brute force and dictionary attacks .
It normally gains access to these hashes from directories, network servers, or domain controllers. It is capable of doing hash extraction from 32 & 64 bit Windows systems, multiprocessor algorithms, scheduling, and can also perform decoding and monitoring networks. Yet it is still the easiest to use password auditing and recovery software available.
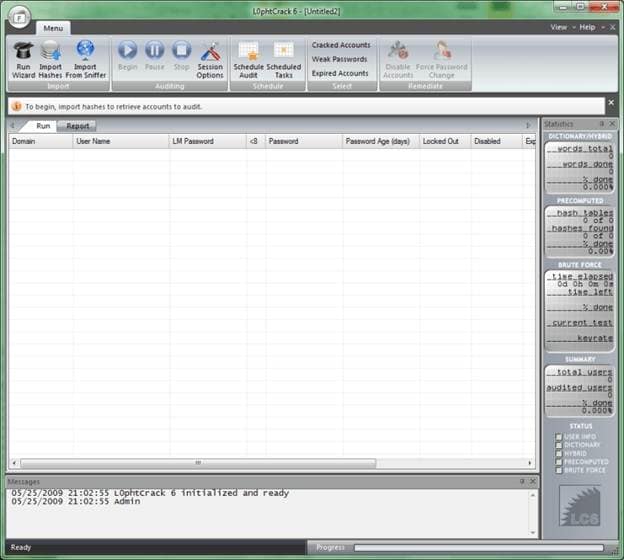
Features of L0phtCrack
- Available for Windows XP, NT, 2000, Server 2003,and Server 2008
- Can work in both 32- and 64-bit environments
- Extra feature of schedule routine auditing on daily, weekly, monthly bases
- After run it provide complete Audit Summary in report page
Site for Download:
9. Pwdump : Password recovery tool for Windows
Pwdump is actually different Windows programs that are used to provide LM and NTML hashes of system user accounts.
Pwdump password cracker is capable of extracting LM, NTLM and LanMan hashes from the target in Windows, in case if Syskey is disabled, software has the ability to extract in this condition.
Software is update with extra feature of password histories display if history is available. Extracted data will be available in form that is compatible with L0phtcrack.
Recently software is updated to new version called Fgdump as Pwdump not work fine when any antivirus program is running.
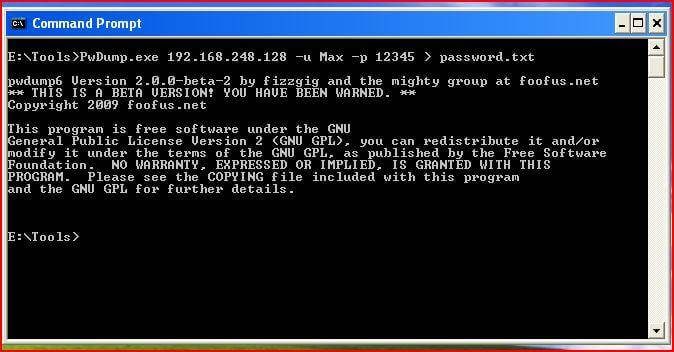
Features of Pwdump
- Available for Windows XP, 2000
- Powerful extra feature are available in new version of Pwdump
- Ability to run multithreaded
- It can perform cachedump (Crashed credentials dump) and pstgdump (Protected storage dump)
Site for Download:
10. Medusa : Speedy network password cracking tool
Medusa is remote systems password cracking tool just like THC Hydra but its stability, and fast login ability prefer him over THC Hydra.
It is speedy brute force, parallel and modular tool. Software can perform Brute force attack against multiple users, hosts, and passwords. It supports many protocols including AFP, HTTP, CVS, IMAP, FTP, SSH, SQL, POP3, Telnet and VNC etc.
Medusa is pthread-based tool, this feature prevent unnecessarily duplicate of information. All modules available as an independent .mod file, so no modification is required to extend the list that supports services for brute forcing attack.
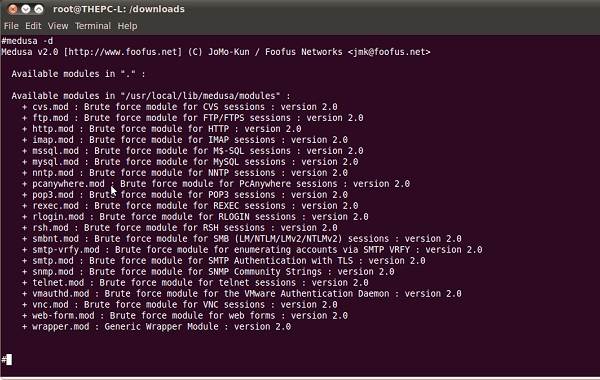
Features of Medusa
- Available for Windows, SunOS, BSD, and Mac OS X
- Capable of performing Thread based parallel testing
- Good feature of Flexible user input
- Due to parallel processing speed of cracking is very fast
Site for Download:
Also read:
- [New] 2024 Approved Live Recording Analyzer
- [Updated] Blur Borders for Visual Privacy
- [Updated] In 2024, A Film Producer's Essential Guide to Color Grading with Standardized LUTs
- From Peak to End: Unveiling the History of Yahoo! Messenger's Shutdown
- In 2024, How To Change Sony Xperia 5 V Lock Screen Clock in Seconds
- In 2024, How to Unlock Motorola Moto G 5G (2023) Phone Password Without Factory Reset?
- In 2024, The Top 5 Android Apps That Use Fingerprint Sensor to Lock Your Apps On Gionee
- Mastering Lock Screen Settings How to Enable and Disable on Motorola G54 5G
- NieR: Shadow Complexes Stutter Bug Fixed: A Comprehensive Guide
- Top 12 Prominent HTC U23 Fingerprint Not Working Solutions
- Top 12 Prominent Motorola Moto G84 5G Fingerprint Not Working Solutions
- Tutorial: Casting Your Favorite TikTok Creators From Smartphone to Television
- Ultimate Guide to Catch the Regional-Located Pokemon For Oppo Reno 10 Pro 5G | Dr.fone
- Updated Best Text Motion Tracking Software for 2024
- Title: How To Enable USB Debugging on a Locked Lava Yuva 2 Phone
- Author: Peter
- Created at : 2025-01-21 16:03:01
- Updated at : 2025-01-23 16:04:36
- Link: https://android-unlock.techidaily.com/how-to-enable-usb-debugging-on-a-locked-lava-yuva-2-phone-by-drfone-android/
- License: This work is licensed under CC BY-NC-SA 4.0.